Another one may crack everything that one human ever created. This sentence, in different alterations, is often used by computer pirates. Programs cracked by them can be easily downloaded on the Internet. Of course, the main advantage of cracked apps is that they are completely free. This factor is a reason for cracked games’ popularity in 3rd world countries. But didn’t you think that computer pirates want to have money to live, too? To have this essential option, they profit in other illegal and possibly harmful ways. Let me explain which ways I am talking about and why using unlicensed games is bad.
Specifying the cracked gfames origins
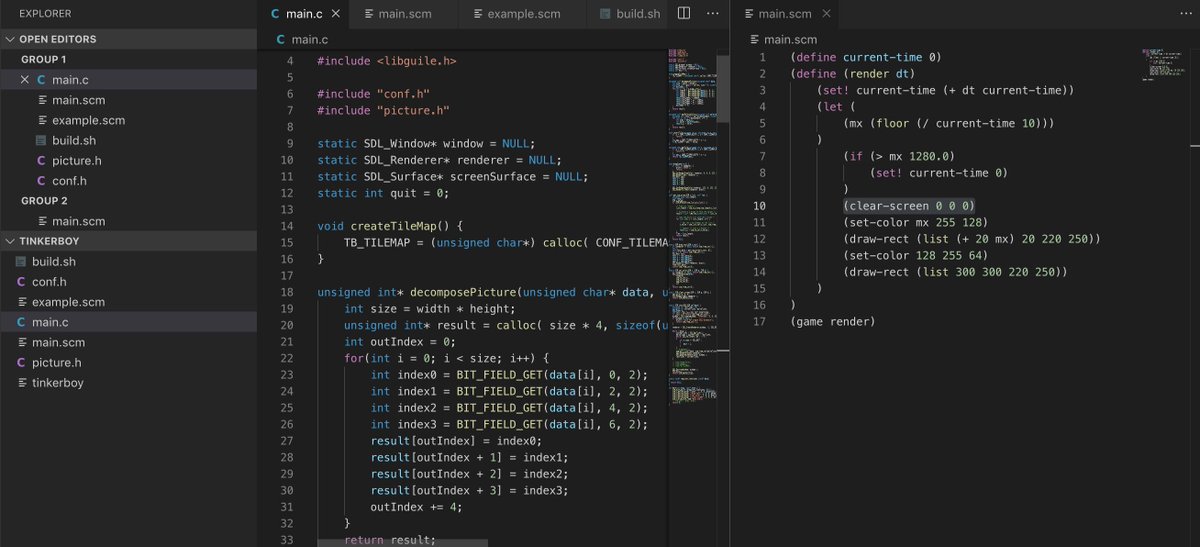
Every not-freeware program has its own license checking mechanism. Such a check may be performed exclusively on the user’s PC and using a PC and a server where all data about licenses is stored. But the code responsible for this operation is stored inside the program’s root directory. Hence, a hacker is able to find this code and modify it in a specific way : he creates a specific “jump” on the license checking stage, so the operation will be simply skipped, and the program will think it is activated1.
Why are cracked programs dangerous?
- Exposed to a range of cyberattacks.
- Adware infections.
- Third-party crypto mining viruses.
- Search engines aren’t safe.
- Phishing attacks.
After the described modification hacker can distribute his program for the wide pirate public. However, he will not have any profit in such a scenario. To solve this problem, hackers add several programs to the initial package. Which programs? Ones whose developers agreed to pay the pirate for this operation. And here goes the most interesting.
Many small developers distribute their programs as a part of the games bundle. It can be whatever – antiviruses (Segurazo, Santivirus, McAfee, Avast, et cetera), “fast and comfortable browsers”, different utilities with or without practical use, etc. Such apps are more annoying than harmful, but their usage may be dangerous because of wrong actions in tight places, like the registry or Group Policies.
But, besides free trash bag-like apps, computer pirates can add different malicious apps. And their type and severity depend only on the size of the reward promised to the hacker by malware developers. It may be something non-critical, like adware or browser hijacker. However, in most cases of malware injection through the cracked games, users get a full-house: trojan-stealer, trojan-backdoor, trojan-downloader, worm, virus, and, finally, ransomware. Because of modern trends through malware, you will get every malware mentioned earlier inside the single app. Bad perspective, isn’t it?
Breaking the law with cracked programs
Using cracked games is an outlaw action in all civilized countries. And if you use it on your home computer and do not create any commercial product with the pirated programs, you may keep calm – it is tough to detect that you use exactly unlicensed games. However, the executive authorities can check big companies and any other commercial organization. And in case cracked games usage is confirmed, the corporation will receive a large fine. The size of this fine is usually much bigger than the license cost for all games that has been used in its cracked version. So, think well before using cracked AutoCAD or Photoshop in your company.

Download games without any risks
There are a variety of ways to download games without exposing yourself to any risk. Here are some tips on how to practice safe gaming:
- Download games from official stores only.
- Avoid buying games from bizarre locations like forums or random pages.
- Learn how to protect your accounts on gaming platforms like Twitch, Discord, Origin, Battle.net, and Steam. Many of them offer two-factor authentication, allowing you to protect your device from unauthorized access even further.
- Check the security features on the platforms you use.
- Always try to download the platform’s official app.
- Use an antivirus for PC when going online and downloading anything.
- Use a reputable antivirus program on all your devices and never disable it.
As you can see, cracked games usage carries many disadvantages that can cost you much more than the license for this program. Yes, in some cases, cracked games usage can be forced – for example, if you want to test the program before purchasing, being not sure if it can satisfy your needs. But even in such a situation – pirating with good intentions – you can become a victim of malware attacks.
- Games cracking process described on Wikipedia


Very good post. I’m facing a few of these issues as well..
This is a good blog.