Security expert Peter Dantini discovered that the Shlayer malware bypassed Apple’s checks: it successfully passed the software notarization process and could run on any Mac running macOS Catalina and newer.
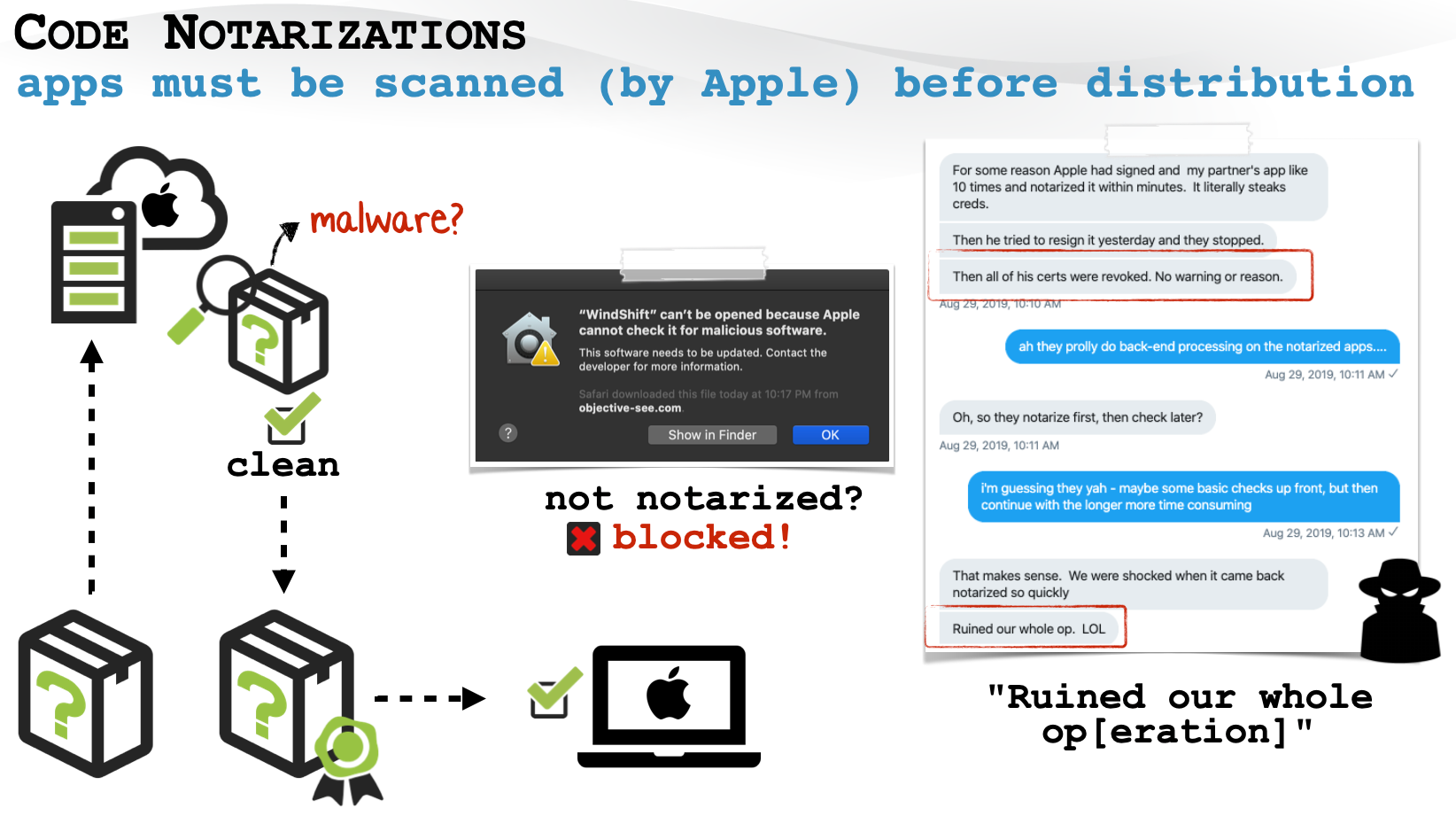
In February of this year, Apple introduced a new security mechanism: any Mac software distributed outside the App Store must go through a notarization process in order to run on macOS Catalina and above.
“Basically, any software for the Mac now has to go through an automated scan at Apple for malware and code signing issues. If the checks are passed, the Gatekeeper allows the application to run on the system”, – explained Apple experts.
On Twitter, Peter Dantini writes that Apple’s automated checks do not seem to be very reliable. The researcher discovered that Shlayer malware installers were distributed through the malicious site Homebrew, which had passed the notarization (as usual, under the mask of updates for the Adobe Flash Player). Therefore, they could be run even on the latest macOS 11.0 Big Sur.
Dantini’s find was confirmed by another well-known expert, Patrick Wardle, who writes in a blog that he immediately notified Apple of the notarized malware, and the company revoked Shlayer’s certificates on the same day, August 28, 2020. This means that the Gatekeeper will now automatically block them.
However, over the last August weekend, a researcher found that the Shlayer campaign was still picking up steam, with offering users new notarized payloads the same day Apple revoked the original certificates. World writes that the old and new payloads are almost identical – they contain OSX.Shlayer, also Bundlore adware.
“It is obvious that in the endless game of cat and mouse between malefactors and Apple, malefactors are still winning”, — concludes the expert.
According to Kaspersky Lab, Shlayer has been the most widespread threat for macOS for two years now: in 2019, every tenth user of the company’s security solutions encountered this malware at least once, and its share in relation to all detections on this OS is almost 30%.
The first copies of the Shlayer family fell into the hands of researchers back in February 2018. At the beginning of 2020, almost 32,000 different malicious Trojan samples were collected, and were identified 143 C&C domains.
Most often, Trojans of the Shlayer family download and install various adware applications on the user’s device. In addition, their functionality theoretically allows downloading programs that not only flood users with advertisements, but also spontaneously open advertising pages in browsers and replace search results in order to download even more advertising messages.



