Microsoft experts talked about the new Android ransomware AndroidOS/MalLocker. (hereinafter simply MalLocker), which easily tricks Russians by pretending to be a screen lock from the police.
Android ransomware abuses the mechanisms behind incoming call notifications and the Home button.
“This malware is hidden inside applications that are distributed through various forums and third-party sites. Like most mobile ransomware, MalLocker does not encrypt user files, it simply blocks access to the phone”, – say Microsoft experts
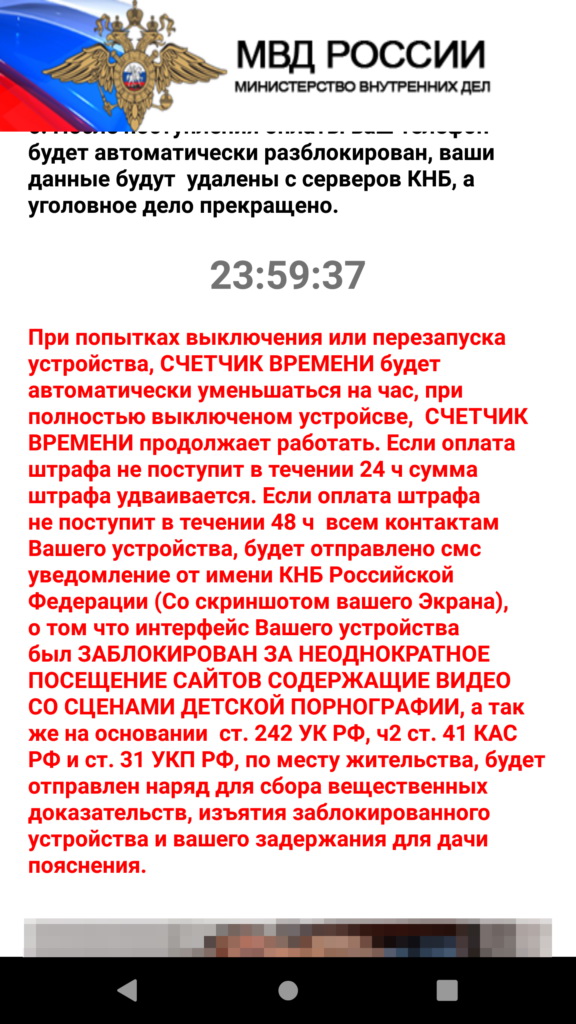
Once on the device, MalLocker captures the screen, locks it and demands a ransom from the victim, claiming that the user has visited child pornography sites and must pay a fine.
To make the threat look more impressive, the malware pretends to be the Ministry of Internal Affairs of the Russian Federation. It should be noted that this is not a new tactic at all, and ransomware often frighten users with law enforcement agencies. However, for some reason, it works especially effectively in Russia.
“If payment of the fine is not received within 48 hours, a notification will be sent to all your phone contacts on behalf of the Russian National Security Committee (with screenshots of your screen) that the interface of your device has been blocked for repeated visits to sites containing videos with scenes of child pornography”, – said in the message of cybercriminals.
The technical side of MalLocker is slightly different from most of these threats. For example, ransomware usually abuses the System Alert window or disables functions that are responsible for interacting with the physical buttons of the device.
MalLocker, in turn, acts differently.
First, it abuses the incoming call notification. This feature is activated when receiving incoming calls and is responsible for displaying detailed information about the caller. Malware uses it to display a window that completely covers the entire screen.
Second, the blocker abuses the onUserLeaveHint() function, which is triggered when the user wants to put the application in the background and switch to another application. It is launched when buttons such as Home or Recents are pressed. The malware uses this feature to keep the ransom note always in the foreground, preventing the user from returning to the home screen or switching to another application.
“Interestingly, this tactic is new and almost unique. For example, ransomware used to only abuse the functionality of the Home button (eg DoubleLocker), but usually combined this with the use of the Accessibility service”, — write Microsoft researchers.
The researchers write that while the MalLocker code is too simple and clearly malicious, so the ransomware cannot penetrate the Google Play Store. However, experts remind that users should avoid installing apps from third-party sources such as forums, websites or unofficial app stores.
Let me remind you that Elon Musk confirmed an accident, when the Russian offered a Tesla employee a million dollars for hacking the company.
And for some reason, I also want you after reading the news about a Russian extortionist who pretends to be a police service, to read about the vulnerabilities in Chinese men’s chastity belts. I don’t know why this is so)



