Pen Test Partners analysts have studied an extremely unusual device: the Cellmate male chastity belts, manufactured by the Chinese company Qiui. So Cellmate chastity belts turned out to be quite vulnerable to external access.
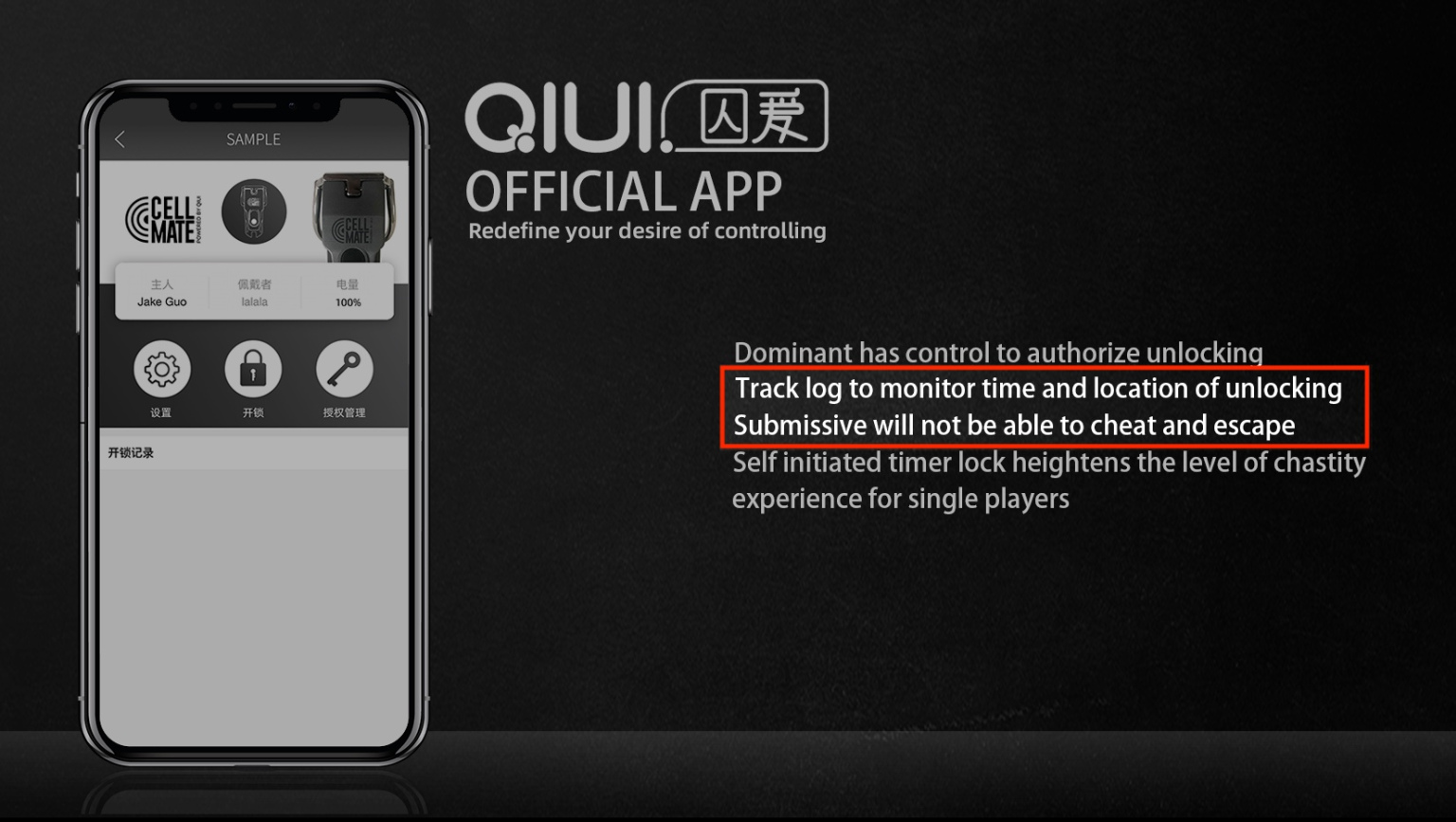
Such gadgets allow owners to entrust access to their genitals to a partner who can lock and unlock the device remotely using Bluetooth and a special application.
However, as experts have found out, due to numerous security problems, such devices can be remotely blocked and opened by hackers, and there is simply no manual control for “emergency” opening or a physical key for Cellmate. That is, blocked users will find themselves in an extremely unpleasant situation.
Researchers have checked and reported that opening the locked device can only be done with a bolt cutter or grinder, cutting the steel bow, but the matter is complicated by the fact that steel bow is located around the testicles of the owner of the gadget.
The device will also open in case of an overload of the board that controls the operation of the lock, and for this you will need to apply approximately three volts of electricity to the device (two AA batteries).
“Over the years, we and other researchers have repeatedly found similar problems with different manufacturers of sex toys. Personally, I believe that such intimate devices should meet higher safety standards than any light bulb”, — says Alex Lomas, an expert at Pen Test Partners.
Interestingly, researchers informed the manufacturer of Cellmate’s devices about security concerns back in April this year. And if at first the representatives of Qiui willingly made contact, then it turned out that the company’s engineers could not completely eliminate the vulnerability, and since then Qiui stopped responding to letters from specialists.
The main problem with Cellmate is its API, which is used to communicate between a gadget and a dedicated mobile application. The API turned out to be open to anyone and is not password protected, and because of this, anyone can take control of any user’s device. This will not only allow hackers to remotely control the Cellmate, but it will also help to gain access to the victim’s information, including location data and passwords.
Qiui engineers updated their app in June in an effort to fix the bug, but users who are using older versions are still vulnerable to attacks. Alex Lomas explains that the developers are in a quandary right now. If they completely disable the old API, it will fix the vulnerability, but then users who have not already updated the application will be blocked. If the API continues to work, older versions of the application will be vulnerable to attacks.
Qiui CEO Jake Guo told TechCrunch that a full bug fix is due in August, but that deadline has passed and there is still no solution to the problem. In one of his letters, Guo told reporters that “fixing will only create more problems.”
As a result, after several months of communication with the developers, Pen Test Partners analysts decided to publish information about the Cellmate problems, hoping that this would contribute to their complete fix. Information security experts do not specifically disclose all the details about the vulnerability so that hackers do not take
advantage of it.
However, according to TechCrunch, this vulnerability is the least of the problems for owners of such devices. Judging by the reviews in the Apple App Store and Google Play Store, leaved by users of the Cellmate mobile application, it often may spontaneously stop working.
“The app completely stopped working after three days and I was stuck!” writes one user. “This is a DANGEROUS program!” Warns another owner of Cellmate. Another one-star review says: “After the update, the app stopped opening the device. This is terrible considering that we trust it and there is no explanation on the [manufacturer’s] website.” Another victim complains: “My partner is locked up! This is outrageous as it is still unknown if this will be fixed and there are no new email responses. Very dangerous! And scary! Given what this application controls, it must be reliable.”
“Hopefully, in the future, some countries and states will start introducing standards for IoT products, but for now, just search for the “product name + vulnerability” or search for security pages on the manufacturer’s website (and not just clichés about “military grade encryption”)”, — advises Alex Lomas.
It must be said that the safety of sex toys and other intimate devices, unfortunately, really leaves much to be desired and is no different from most other IoT devices. And those vulnerabilities are enough. And I have already told about some rather curious ones. For example, recently Avast expert taught Smarter Coffee machine to ransom money, and a little earlier vulnerabilities in Amazon Alexa opened access to user data for outsiders.



