The well-known information security expert, journalist and author of the KrebsOnSecurity blog has repeatedly become a target for attacks and mockery of hackers. Now hackers are attack Microsoft Exchange servers with Proxylogon vulnerabilities on behalf of Brian Krebs.
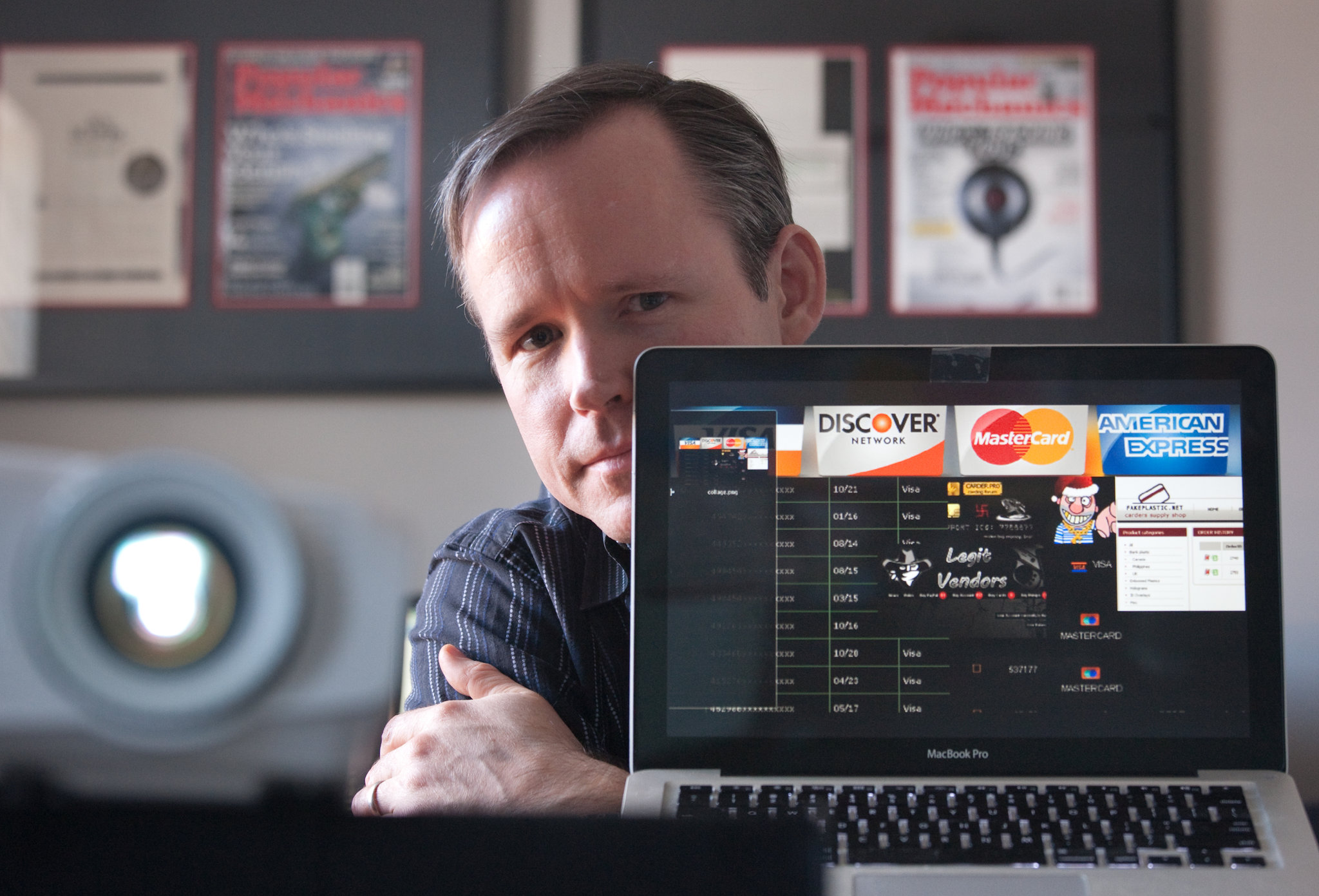
The fact is that Krebs is famous for his investigations and revelations, and over the long years of his career, he helped find and de-anonymize more than a dozen criminals, which the latter, of course, do not like at all.
Criminals have been taking revenge on the journalist for many years. So, criminals have been already sent a SWAT team to Krebs home, they took a loan on his behalf for $20,000, transferred $1,000 to his PayPal account from a stolen payment card, and the PayPal account itself was compromised more than once. They even tried to transfer money from Krebs’ account to the terrorist the ISIS subsidiary. After disclosure of the Mirai IoT malware authors, Krebs’ website suffered one of the most powerful DDoS attacks in history at that time.
A couple of years ago, users of the German imageboard Pr0gramm (pr0gramm.com), with which the operators of the Coinhive cryptojacking service were associated, standed against the journalist. Offended by the Krebs investigation, users launched the #KrebsIsCancer campaign on social networks (“Krebs is cancer”). The fact is that in German the surname of the journalist, Krebs, translates as “cancer”, and on Pr0gramm they decided to literally “fight cancer”: they trolled Krebs and eventually donated more than $120,000 to this fight.
It is also worth noting that malware authors often mention Brian Krebs in the code of their programs as a kind of “hello”. According to the journalist, a complete list of such cases would consist of hundreds of pages.
Yesterday there was a post on KrebsOnSecurity titled “No, I Didn’t Hack Your MS Exchange Server“. In it, Krebs says that now “on his behalf” attacks are taking place on servers that are vulnerable to ProxyLogon problems.
The researcher writes that the Shadowserver Foundation found that Microsoft Exchange servers are being attacked by the KrebsOnSecurity and Yours Truly malware.
For example, the attackers first host the Babydraco web shell on the vulnerable server at /owa/auth/babydraco.aspx. The malicious file krebsonsecurity.exe is then loaded via PowerShell, which transfers data between the victim server and the attacker’s domain – Krebsonsecurity[.]top.
Shadowserver has found more than 21,000 Exchange servers running the Babydraco backdoor, although they do not know how many of those systems were downloading secondary payloads from a rogue version of Krebsonsecurity.
The researcher cites the December post of one of the website visitors:
Krebs explains that instead of “XXX-XX-XXX”, that address was his social security number. “I was killed through DNS,” he sums up.
Let me also remind you that we reported that Researcher Published PoC Exploit for ProxyLogon Vulnerabilities in Microsoft Exchange.