Scientists talked about how to make fraudulent payments using Apple Pay with a Visa card on a locked iPhone. This scam works over the air, even if the iPhone is in your bag or pocket, and has no limit on the number of transactions. A report on this issue [PDF] will be presented at the IEEE 2022 Symposium.
Their research was published by the University of Birmingham and the University of Surrey, who found that the iPhone can confirm almost any transaction under certain conditions. Typically, for the payment to go through, the iPhone user needs to unlock the device using Face ID, Touch ID, or a passcode. However, in some cases this is inconvenient, for example, when paying for public transport fares. For such cases, Apple Pay provides Express Transit, which allows making transactions without unlocking the device.
Express Transit, for example, works with transport turnstiles and card readers that send a non-standard byte sequence bypassing the Apple Pay lock screen. The researchers say that in combination with a Visa card, “this feature can be used to bypass the Apple Pay lock screen and make illegal payments from a locked iPhone, using any EMV reader, for any amount and without user authorization.”
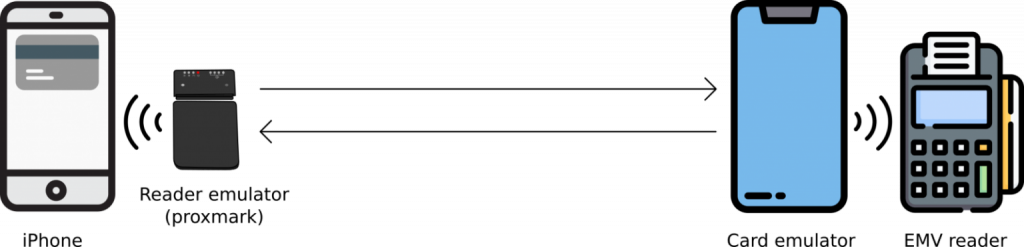
For example, experts were able to simulate a transaction at the turnstile using a Proxmark device that acts as a card reader, which communicated with the target iPhone, as well as an Android smartphone with NFC, which communicated with the payment terminal.
In essence, this method is a replay and relay MitM attack in which Proxmark plays back iPhone magic bytes to trick the device into believing it is a transaction at the turnstile, so no user authentication is required to authorize the payment.
Digging deeper into the problem, the researchers found they could change the Card Transaction Qualifiers (CTQ), which are responsible for setting limits for contactless transactions. Thus, it was possible to trick the card reader so that the authentication on the mobile device was successfully completed.
As a result of the experiments, the researchers were able to make a transaction of £1000 from a locked iPhone, and successfully tested such an attack on the iPhone 7 and iPhone 12.
At the same time, it is noted that the tests were successful only with iPhone and Visa cards (in the case of Mastercard, a check is performed to make sure that the locked iPhone carries out transactions only with card readers, for example, in transport). By examining Samsung Pay, the researchers concluded that transactions with locked Samsung devices are possible, but the value is always zero, and transportation providers charge tolls based on the data associated with these transactions.
Experts say that they submitted their findings to Apple and Visa engineers in October 2020 and May 2021, but the company still has not fixed the problem.
Visa officials told Bleeping Computer the following:
Let me remind you that I reported that Scientists have developed an attack that allows not to enter a PIN code while paying with Visa cards.