Sansec experts have discovered a new multi-platform MageCart skimmer capable of stealing payment information from compromised stores. The web skimmer works in Shopify, BigCommerce, Zencart and Woocommerce stores (even if they don’t support custom scripts for checkout pages).
Let me remind you that initially the name MageCart was assigned to one hack group, which was for the first time used web skimmers (malicious JavaScript) on the pages of online stores to steal bank card data.
However, this approach was so successful that soon the group had numerous imitators, and the name MageCart became a common name, and currently denoting a whole class of such attacks.
Sansec analysts have identified the new malware in dozens of stores across different platforms. The malware steals payment information by displaying a fake checkout page (before customers see the actual payment form) and also uses a keylogger for card data and personal information.

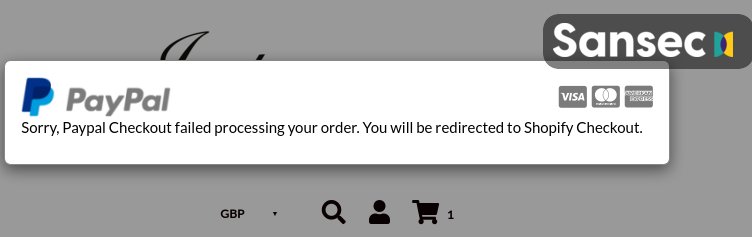
To avoid detection, the skimmer displays an error after customers click the Continue button to provide the store with their credit card information. After that, the victims will be redirected back to the real ordering and payment form.
The method of data extraction used by the skimmer is also remarkable. Attackers use for this purpose automatically generated domains based on counter and base64 (for example, zg9tywlubmftzw5ldza[.]com and zg9tywlubmftzw5ldze[.]com). This feature helped researchers understand how long this campaign has been active: the first domain for data extraction was registered on August 31, 2020.
Let me also remind you that Hackers hide MageCart skimmers in social media buttons.
For a newer WooCommerce-specific example, Gridinsoft also covered FunnelKit checkout skimmer attacks, where malicious scripts were added through store funnel configuration rather than only through changed site files.



