Microsoft analysts have discovered a malicious campaign, in which hackers force users to solve CAPTCHA before they gain access to malicious content in an Excel document. This file contains macros that install on the victims’ machines GraceWire Trojan, which steals confidential information (for example, passwords).
Responsibility for this campaign is put on the hacking group Chimborazo, which experts have been observing since January this year.
This campaign was named Chimborazo Dudear. Initially, hackers acted according to the classical scheme and applied malicious Excel documents to phishing emails. Then they switched to links embedded in messages. In recent weeks, the group began sending out phishing emails containing links to redirecting sites (usually legitimate resources that were hacked), and sometimes an HTML attachment containing a malicious iframe is attached to the emails.
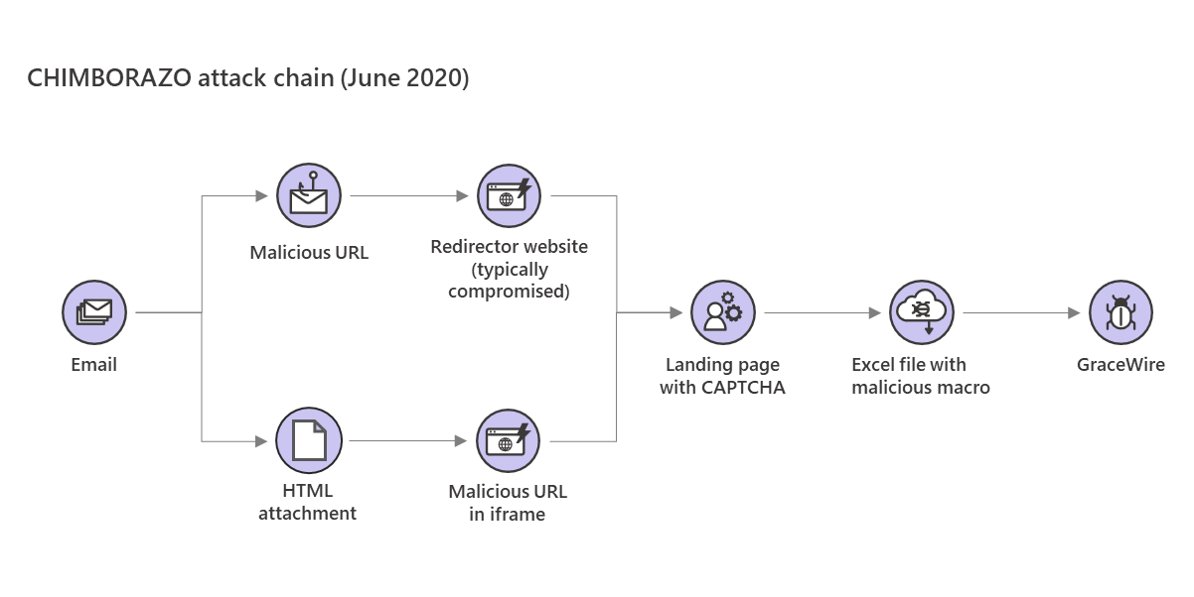
By clicking on such a link or opening an attachment, the victim will in any case be taken to the site with the download of a malicious file. However, before accessing the file itself, the user will be forced to solve CAPTCHA.
Thus, the attackers tried to impede the work of automatic defense mechanisms, which should detect and block such attacks. Typically, this analysis is performed using bots that download malware samples, run them, and analyze them on virtual machines. CAPTCHA guarantees that a living person will load the malware sample”, — say Microsoft analysts.
Let me remind you, that by the way, 82.5% of Microsoft Exchange servers are still vulnerable.
In January of this year, Security Intelligence specialists already wrote about the attacks by the Chimborazo group. Researchers then said that a hacker group uses IP address tracking to identify computers from which they downloaded a malicious Excel file. Presumably, this was also done in order to avoid automatic detection.
Malwarebytes expert Jérôme Segura writes that the use of CAPTCHA by hackers is a rare but not unprecedented case. For example, he refers to a tweet from another information security specialist, dated late December 2019. Then, was also discovered a fake CAPTCHA, which the attackers successfully used to complicate the work of automatic analysis.
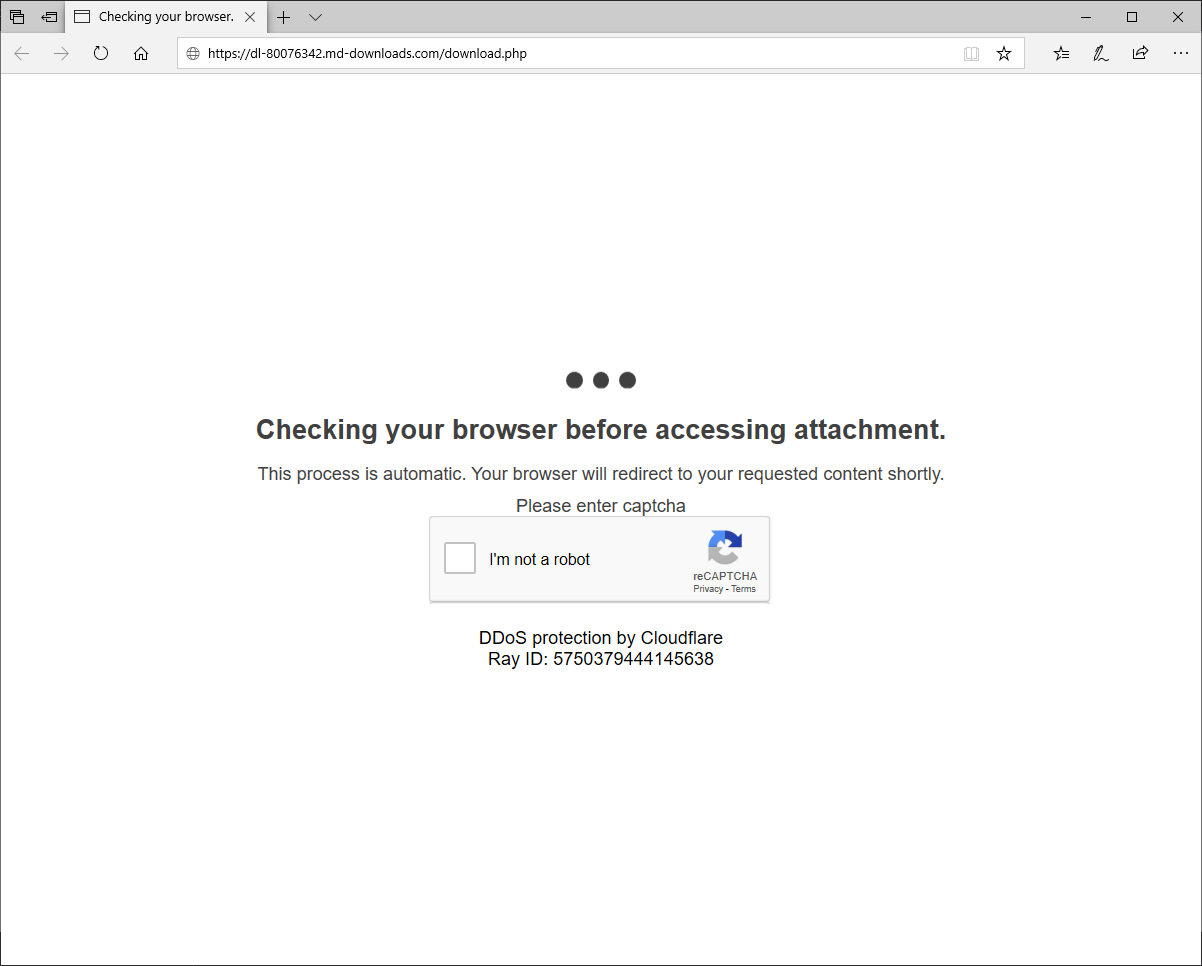
Discovered by Microsoft CAPTCHA may also be fake. As you can see in the picture above, the attacker site claims to use reCAPTCHA, but below it is stated that Cloudflare provides protection against DDoS attacks. These are two separate services, although it is possible that the hackers used both separately.