Last weekend, one of Argentina’s largest internet providers, Telecom Argentina, suffered from REvil (Sodinokibi) ransomware attack. Malware has infected about 18,000 computers, and now REvil operators demand $7.5 million from the company.
The ZDNet magazine writes that the attackers managed to gain domain administrator rights, thanks to which the ransomware quickly spread to 18,000 workstations.
“Oddly enough, this incident did not lead to problems with the Internet connection for the provider’s customers and did not affect the operation of telephony and cable TV services. However, due to the consequences of the attack, a number of Telecom Argentina’s official websites are still not working”, – according to journalists ZDNet.
Several employees of the affected company share on social media how the provider is coping with the crisis. It seems that immediately after the attack was detected, the company began to warn employees about what was happening, asking them to limit interaction with the corporate network, not to connect to the internal VPN network, and not to open emails with archives in attachments.
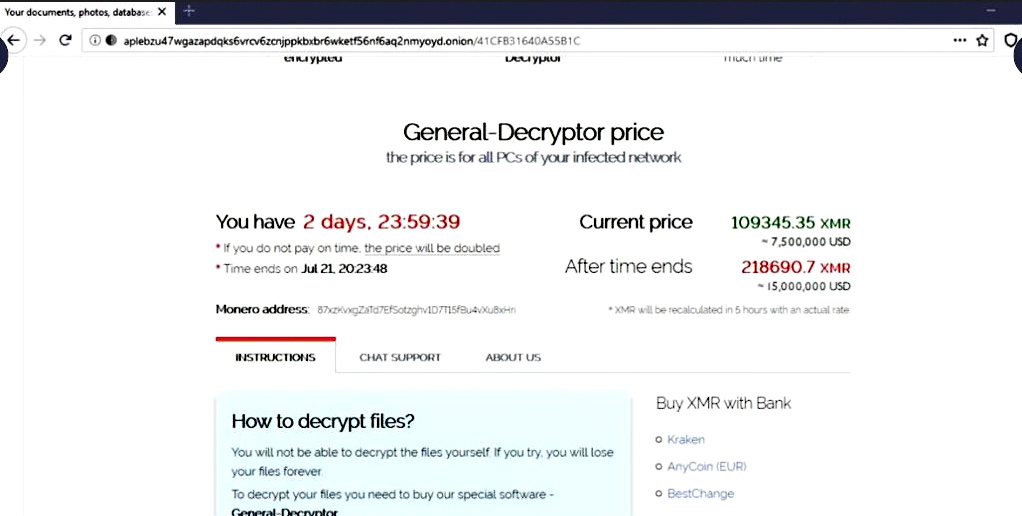
Reporters think that responsibility o the attack lies on the REvil hack group, based on a tweeted post that showed a screenshot of the ransomware site. Based on this image, the attackers demanded a ransom 109,345.35 Monero (approximately $7.53 million) from the company. The hackers promised that in case of non-payment, this amount would double in three days, making this ransom demand one of the largest this year.
Telecom Argentina officials have not yet commented on the situation, and it is not known whether the company intends to pay the cybercriminals.
Interestingly, according to local media reports, the ISP considers a malicious attachment from a letter received by one of its employees to be the starting point of this attack.
“This is not entirely consistent with regular REvil attacks, as the group usually penetrates companies’ networks through unprotected network equipment. In particular, attackers are actively exploiting vulnerabilities in Pulse Secure and Citrix VPN”, – reported in ZDNet.
However, the specialists of the information security company Bad Packets told ZDNet journalists that Telecom Argentina not only worked with Citrix VPN servers, but among them there were systems vulnerable to the CVE-2019-19781 problem (although the patch was released many months ago).
let me remind you that, information security specialists of the Danish provider KPN applied sinkholing to REvil (Sodinokibi) cryptographic servers and studied the working methods of one of the largest ransomware threats today. A very interesting analysis – I recommend it.



