Bitdefender experts gave a detailed description of the work of the P2P botnet Interplanetary Storm (aka IPStorm), which uses infected devices as a proxy.
According to researchers, the botnet includes more than 9,000 hosts (according to other sources, the number of infected devices exceeds 13,500), the vast majority of which are running Android, and about one percent are running Linux and Darwin.
“These are various routers, NAS, UHD receivers, multifunctional boards (for example, Raspberry Pi) and other IoT devices. Most of the infected devices are located in Hong Kong, South Korea and Taiwan”, – said the researchers.
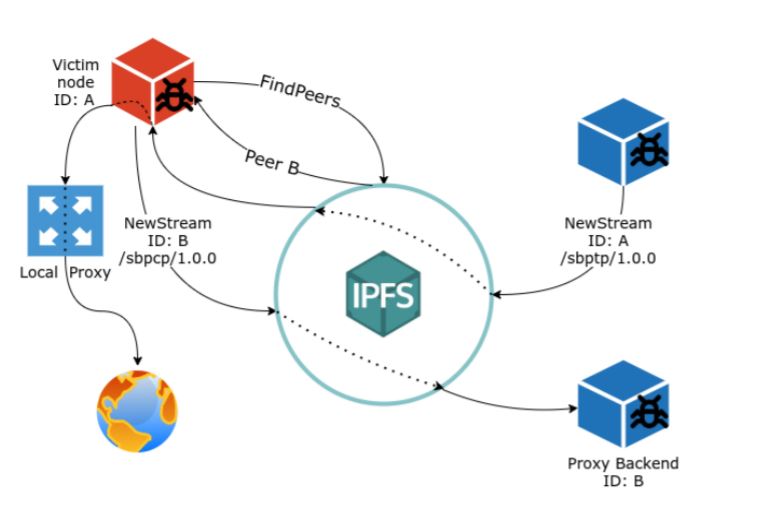
The researchers write that the purpose of the botnet can be guessed by the specialized nodes that are part of the malware’s control infrastructure:
- a proxy server that pings other nodes to confirm their availability;
- proxy checking program that connects to the bot’s proxy server;
- a manager who gives commands for scanning and brute-force;
- backend interface responsible for hosting Web API;
- a node that uses cryptographic keys to authenticate other devices and sign authorized messages;
- node used for development.
Overall, this infrastructure guarantees checking the availability of nodes, connecting to a proxy, hosting a Web API, signing authorized messages, and even testing malware at the development stage, say the researchers.
“This all suggests that the botnet is being used as a proxy network, probably offered as an anonymization service”, — the Bitdefender report says.
Interplanetary Storm is infected through SSH scanning and weak password guessing. The malware itself is written in the Go language, and the report emphasizes that its main functions were written from scratch, and not borrowed from other botnets, as it often happends. In total, the researchers found more than 100 changes in the malware code, therefore, the development of Interplanetary Storm is gaining momentum.
The malware code integrates the implementation of the open source protocols NTP, UPnP and SOCKS5, as well as the lib2p library for implementing peer-to-peer functionality. The malware also uses a lib2p-based networking stack to interact with IPFS.
“Compared to other Go malware we’ve analyzed in the past, IPStorm is notable for its complex design of module interactions and the way it uses libp2p constructs. It is clear that the attacker behind this botnet has a good command of Go”, — the experts summarize.