The Bleeping Computer magazine warns that the new version of the AnarchyGrabber Trojan steals passwords and tokens, disables 2FAs and distributes the malware to the victim’s friends. Moreover, attackers modify and use the official Discord client as a tool for stealing passwords.
As a rule, attackers spread AnarchyGrabber through Discord, posing as a trojan for a game cheat, hacker tool or pirated software. If the victim is caught at this phishing trick, after installing the trojan, it modifies the Discord client’s JavaScript files to turn it into a malware that can steal user’s token. Using this token, hackers get the opportunity to enter Discord under on behalf of their victim.
However, a new version of AnarchyGrabber that was spotted last week, posses a number of new features.
“Now the malware is called AnarchyGrabber3, it steals victims’ passwords in plain text, and can also use the infected Discord client to spread the threat further to all victim’s friends. Passwords stolen in this way can be used to hack accounts on other sites”, – report Bleeping Computer journalists.
After installation, AnarchyGrabber3 uses the %AppData%Discord[version]modulesdiscord_desktop_coreindex.js file of the Discord client to load other JavaScript files added by the malware. As you can see in the illustration below, when you start Discord, a modified script loads a file called inject.js from the new 4n4rchy folder.
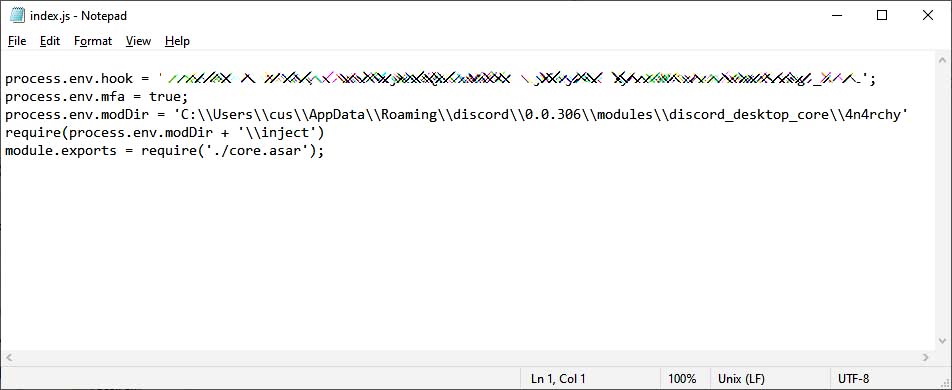
Then this file will load another malicious file into the client – discordmod.js. These scripts log out the user from the Discord client and prompt them to re-enter the application.
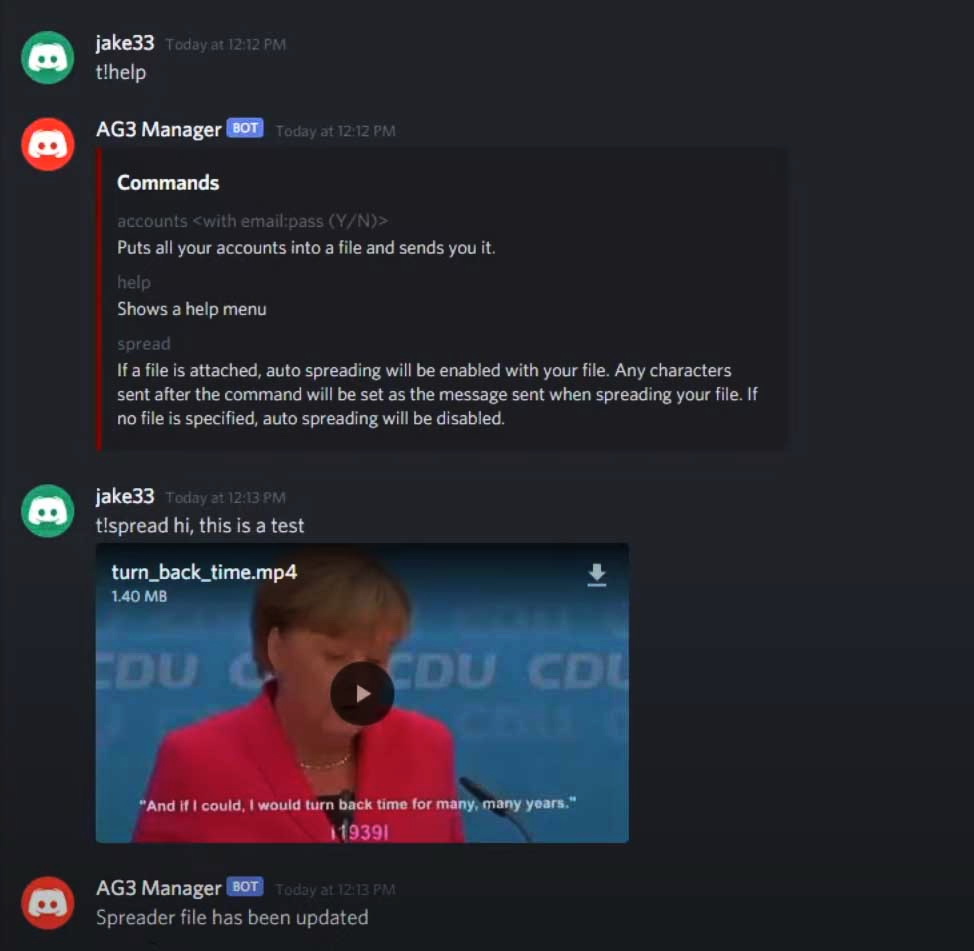
As soon as the victim logs in, the modified Discord client tries to disable two-factor authentication for the account. The client then uses a web hook to send an email address, username, token, plain text password, and IP address to a special Discord channel that control attackers.
After that, the “corrected” Discord client waits for further commands from its operators. One of them may order hacked Discord clients to send malicious messages with the same malware to all the victim’s friends.
Researchers write that this component makes it easier for criminals to spread AnarchyGrabber3, and can also be used to spread other types of malware.
The publication warns that the main danger of AnarchyGrabber is that majority of its victims do not even know that they were infected. So, after launching the AnarchyGrabber3 executable file and changing the Discord client files, the trojan practically does not manifest itself and does not start again. That is, there is simply no malicious process that an antivirus could detect, and an infected computer remains part of the botnet.
In fact, the only way to uninstall AnarchyGrabber3 is to uninstall the Discord client and reinstall it.
In the context of this case I would remind that password meter services also put Internet users at risk.
Related cleanup guide
Related: If Discord started sending celebrity giveaway or crypto messages, see the MrBeast Discord crypto spam recovery guide.