Sophos researchers noticed that the MyKingz botnet, also known as Smominru, DarkCloud, and Hexmen, now uses steganography to infect targeted machines. For these purposes, the criminals chose a JPG file – a photo of the pop singer Taylor Swift.
Experts first discovered the MyKingz botnet at the end of 2017. Since then, it has become one of the largest mining threats in the world.
By the way, find out about the most dangerous malware in November 2019.
Researchers acknowledge that MyKingz has one of the most serious and well-thought-out mechanisms and infections in the “market” of botnets.
“So, the malware does keeps in focus any port that can be scanned, and does not miss a single vulnerability that can be exploited. Everything from MySQL to MS-SQL, from Telnet to SSH, and from RDP to rarer things like IPC and WMI is at the forefront of the botnet”, – say Sophos experts.
Because of this approach, the botnet has grown very quickly. Therefore, it was reported that only in the first months of its existence, MyKingz infected more than 525,000 Windows systems, bringing its operators more than $ 2.3 million (about 8900 Monero).
What is worse, since malware developers often use the EternalBlue exploit, the threat often penetrates corporate networks, which means that the actual size of the botnet and the proceeds of criminals are likely to be much higher than the figures estimated by the experts.
“MyKingz’s operators currently receive about $ 300 a day, bringing their total revenue to about 9,000 XMR, which at the current rate is more than $ 3 million”, – this is how Sophos Researchers assess MyKingz Botnet.
Although some experts thought that the botnet had ceased to exist, reports by Guardicore and Carbon Black published this summer showed that the botnet is still alive and infects many computers: about 4700 new systems per day.
Now, Sophos experts have noticed that changes have again appeared in the botnet’s behavior. Since the MyKingz scanning module only detects vulnerable hosts and secures itself to infected computers, hackers also need a way to deploy malware into hacked systems. To do this, MyKingz operators are currently experimenting with steganography: a malicious EXE file is hidden inside a JPG image with a photo of singer Taylor Swift.
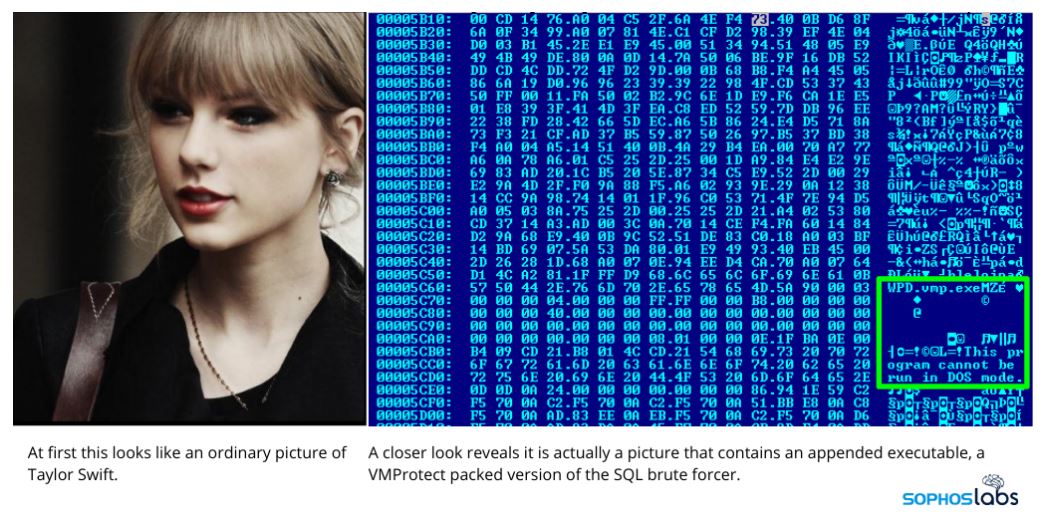
This is done to deceive the security software that works in corporate networks.
Therefore, security software “sees” only the simple JPEG file, and not the dangerous EXE file.
Interestingly, this is not the first case of such exploitation of photographs of celebrities. For example, last year another malware used the photo of actress Scarlett Johansson to deliver malware in hacked PostgreSQL databases.
However, to protect the system, it is not enough to not open randomly pictures of cuties like Taylor and Scarlett – remember about having strong reliable password. However, there is also a danger; hence, as we reported, password meter services put Internet users at risk.