Experts from Israel’s Ben-Gurion University have demonstrated the AIR-FI attack, which turns RAM into Wi-Fi. In fact, this is a new method of extracting data from machines that are physically isolated from any networks and potentially dangerous peripherals. Such computers are often found in government systems and corporate networks, they store secret documents, as well as classified and confidential information.
This time, the researchers proposed turning the RAM into an impromptu wireless emitter for transmitting data “over the air.”
Since Wi-Fi is radio waves, which is very close to electromagnetic waves, the researchers write that, in theory, a hacker can manipulate the RAM power to generate electromagnetic waves with a frequency corresponding to the frequency of the Wi-Fi signal (2.4 GHz).
Experts show in their report and accompanying video that carefully controlled RAM read / write operations can cause the memory bus to emit electromagnetic waves similar to a weak Wi-Fi signal.
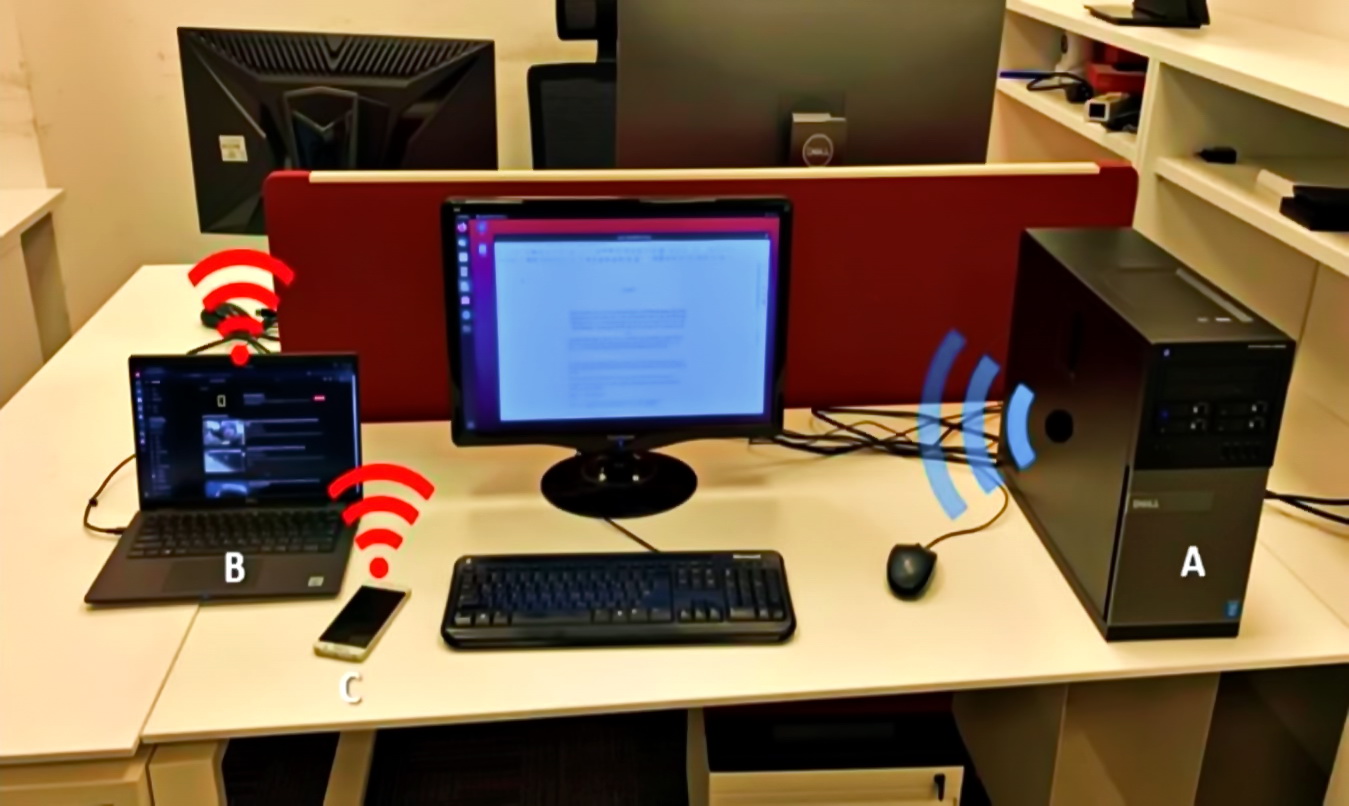
Such a signal can be received by any Wi-Fi-enabled device located near an isolated computer, for example, a smartphone, laptop, IoT device, smart watch, and so on.
The experts tested AIR-FI on various isolated systems and, as a result, were able to transfer data at a speed of up to 100 bps to devices located several meters away from the compromised machine.
AIR-FI is not the first exotic attack developed by specialists from Ben-Gurion University (a list of other attacks can be seen below), but the researchers note that this method is one of the easiest to implement.
Indeed, in this case, the attacker does not need to obtain root / administrator rights before launching his exploit. In essence, this allows the attack to run on any OS and even on virtual machines. It is also noted that most modern RAM strips can easily emit signals in the 2.4 GHz range, and the old memory is easy to overclock to achieve the desired effect.
Other developments of scientists from Ben-Gurion University include the following:
- USBee: turns almost any USB device into an RF transmitter for transferring data from a secure PC;
- DiskFiltration: intercepts information by recording sounds that the hard disk of the computer emits while the computer is running;
- AirHopper: uses the FM receiver in the mobile phone to analyze the electromagnetic radiation emanating from the computer’s graphics card and turn it into data;
- Fansmitter: regulates the speed of the cooler on the infected machine, as a result of which the tone of the cooler’s operation changes, it can be listened to and recorded by extracting data;
- GSMem: will transfer data from the infected PC to any, even the oldest push-button telephone, using GSM frequencies;
- BitWhisper: uses thermal sensors and thermal energy fluctuations;
- An unnamed attack using flatbed scanners and smart bulbs to transmit information;
- HVACKer and aIR-Jumper: stealing data using CCTV cameras that are equipped with IR LED (infrared light-emitting diodes), as well as use as a “bridge” to isolated networks of heating, ventilation and air conditioning systems;
- MOSQUITO: data extraction is suggested to be carried out using ordinary headphones or speakers;
- PowerHammer: It is suggested to use normal power cables for data extraction;
- CTRL-ALT-LED: Caps Lock, Num Lock and Scroll Lock diodes are used to retrieve information;
- BRIGHTNESS: retrieve data by changing the brightness of the monitor screen.
And also, let me remind you that we talked about the fact that specialists from the Ben-Gurion University of Negev (Israel) presented a new type of cyber-biological attack that can bring biological warfare to a new level.