Throughout the timeline of the trojan virus evolution, it obtained a lot of different forms. They have become global malware that can exploit your computer as it wants. In this article, I will tell you about the particular type of trojan virus – Trojan Coin Miners, also known as “Coin Miner Virus”1.
Coin miners: essence, spreading and reasons for appearing
The first trojan virus that could use the infected machine for cryptocurrency mining appeared in 2016. But their appearance was not explosive: there was no reason for their massive distribution. Cryptocurrencies were still unpopular, and their prices were low, so the cyber burglars saw no potential in such a type of malware.
The things changed in 2017 when the first cryptocurrency rush occurred2. Bitcoin reached the $60000 price tag for a single coin, and other crypto coins, like Ethereum, Litecoin, or Ripple, were also at their highs. This type of equity has attracted (and still attracts) the big money, and where big money is, the people who want to have an illegal bite of this money appear.
Peak of trojan-miner activity was reached in March 2018. When the price of Bitcoin shed back to $5000, coin miners’ activity dropped, too. The graphic below can easily prove the strict correlation between miners’ activity and the prices of cryptocurrencies.
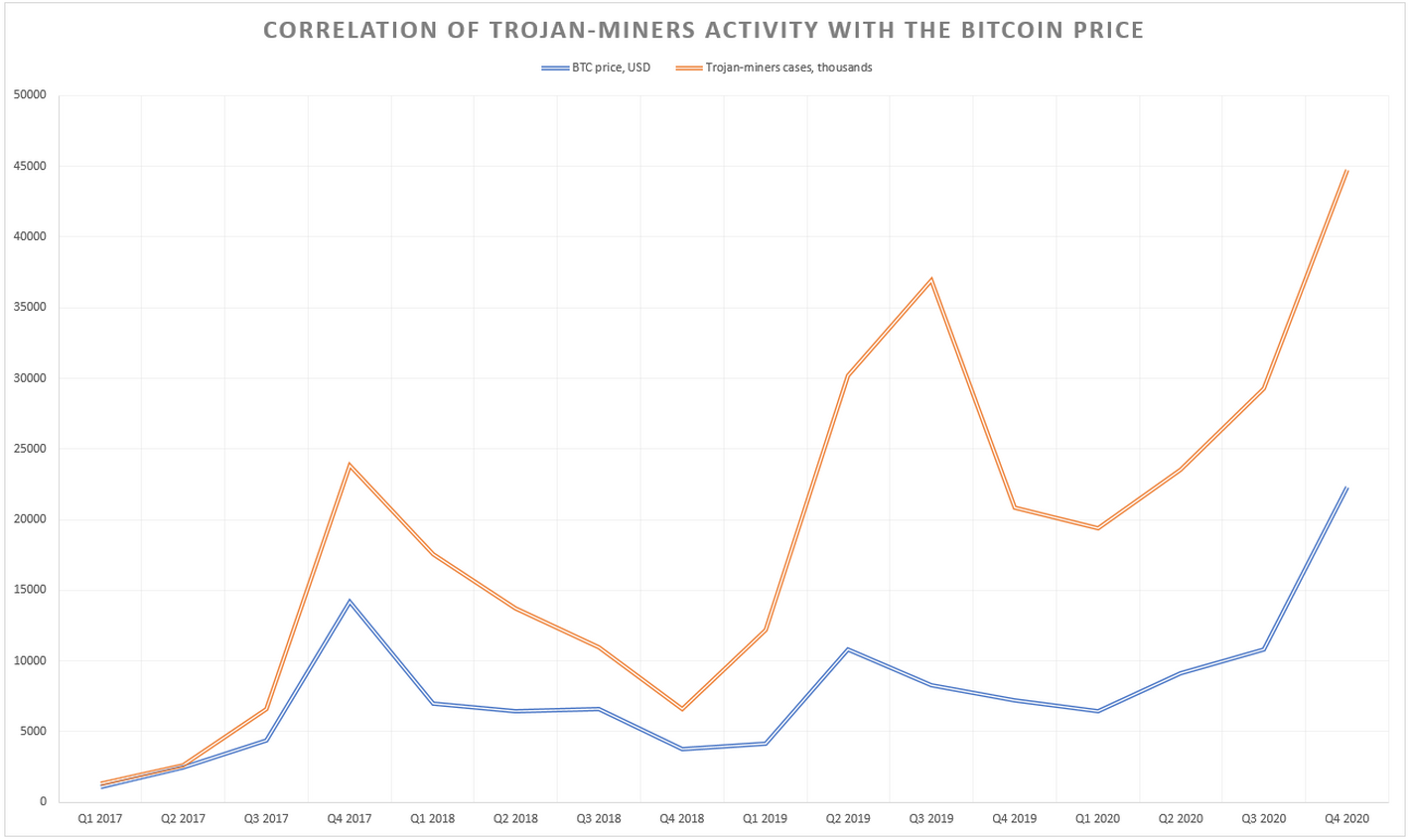
In the summer of 2021, when the cryptocurrency price began pumping again, trojan miners quickly rose to the peak of 2018 and kept going as the Bitcoin price rose to $40000. Nowadays, coin-mining trojans are as active as they have ever been.
How can I detect that my PC is infected with coin miner trojan?
Have you ever tried to use an old computer with fresh Windows? The system freezes on every operation because of the lack of RAM and the slow reading speed of the HDD, so the operating system is forced to load the files from RAM out to the swap file. Coin miners can force you to remember these feelings. Your CPU and GPU are loaded to 100%, regardless of the number of launched programs. Google Chrome opens for more than one minute; attempting to open Photoshop may lead to its crash, and you can do nothing to deal with this problem. And it doesn’t matter if your computer is a high-end PC – even systems with Core i9-12900KF/Ryzen 7 6800H and RTX 3090 will suffer.
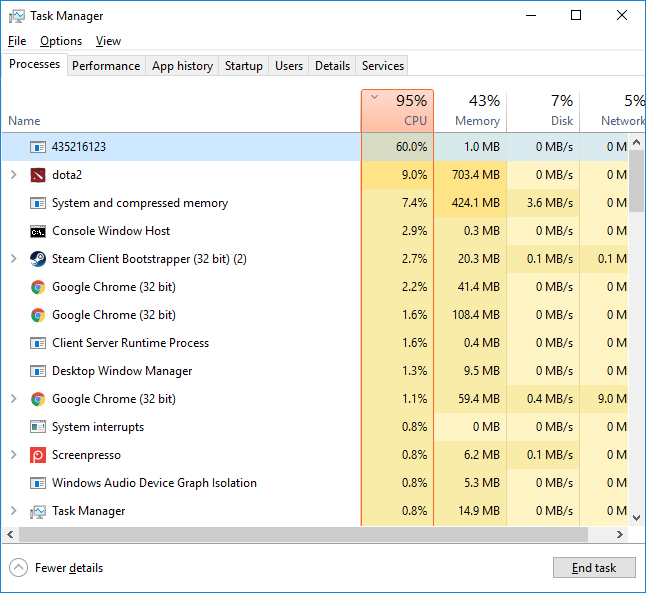
If you have the described symptoms, you have the coin miner in your system. The last thing that can ensure this decision is a strange process in the Task Manager. Sometimes, coin miner developers do not try to hide it, naming the process created as “miner” or “trainer”. Whatever it was, this process will consume an enormous amount of your CPU/GPU capacities, so you will easily distinguish it from other processes.
Are coin miners dangerous?
There is a widespread misconception that coin miners carry no danger to your computer because they load your hardware to the max values. Such a conception may be true for users who regularly check their PC to detect hardware issues, such as dust in the coolers or breaking in the moving parts. But what about the average user who cleans the dust from the cooling fan only after it whines loudly after the PC launch? Or individuals who have a bad/weak power supply, so it generates the pulsating current?3
In the mentioned cases, a long overload with a high chance may lead to the components breaking. The CPU is sensitive to overheating, and it is quite simple to make it boil with a malfunctioning cooling system. Pulsating current is even more dangerous: such voltage volatility can easily break some components and kill the whole motherboard, so you will need to buy a new one besides the broken hardware.
The danger of hardware damage is not the single thing you need to be afraid of. Due to the modern trend of making the virus complex, your PC will likely be infected with numerous other viruses. Choose what you like: spyware, keyloggers, adware, backdoors, and even ransomware. The possible danger that this malware may carry is enormous – data/credentials stealing, file encryption, including your PC to the botnet, remote controlling – that is not a full list of the consequences. It is recommended to scan your computer as soon as possible and remove all malicious items in your system.
- Detailed investigation of the coin mining trojans.
- Cryptocurrency rush description on Wikipedia.
- About the dangers of bad power supply usage.


